Comprehensive SSH IoT Firewall Tutorial For Enhanced Network Security
In today's interconnected world, IoT (Internet of Things) devices have become an integral part of our lives. However, with the rise in IoT adoption, security concerns have also increased significantly. One of the most effective ways to secure IoT networks is by using SSH (Secure Shell) in conjunction with firewalls. This SSH IoT firewall tutorial will guide you step-by-step on how to enhance your network's security by leveraging these powerful tools.
IoT devices are increasingly being targeted by cybercriminals due to their often weak security configurations. As businesses and individuals rely more heavily on these devices, understanding how to secure them becomes crucial. This tutorial aims to provide in-depth knowledge about SSH and firewall integration, empowering users to safeguard their networks effectively.
Whether you're a network administrator or a tech enthusiast, this guide will help you grasp the essentials of SSH IoT firewall implementation. By following the steps outlined here, you'll be able to protect your IoT infrastructure from unauthorized access and potential threats.
Read also:Aaron Carter And Diddy The Untold Story Of Their Connection
Table of Contents
- Introduction to SSH
- Understanding Firewalls
- Why Combine SSH and Firewalls for IoT Security?
- Preparation for SSH IoT Firewall Setup
- Installation of SSH and Firewall
- Configuration of SSH and Firewall
- Testing the SSH IoT Firewall
- Advanced Security Measures
- Troubleshooting Common Issues
- Best Practices for SSH IoT Firewall
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol designed for secure data communication over unsecured networks. It provides strong authentication and encrypted data communications between two computers, making it an ideal choice for securing IoT devices.
Key Features of SSH:
- Encryption of data to prevent eavesdropping
- Authentication mechanisms to ensure secure access
- Support for tunneling, forwarding, and remote command execution
SSH is widely used in network operations to provide secure remote access to servers and devices. By incorporating SSH into your IoT infrastructure, you can significantly reduce the risk of unauthorized access and data breaches.
SSH Versions and Protocols
There are two primary versions of SSH: SSH-1 and SSH-2. SSH-2 is the current standard and offers enhanced security features compared to its predecessor. It supports stronger encryption algorithms and more robust authentication methods.
SSH Protocols:
- Transport Layer Protocol
- User Authentication Protocol
- Connection Protocol
Understanding these protocols is essential for configuring SSH correctly in your IoT environment.
Read also:Unveiling The World Of Movierulz Hd Bar Your Ultimate Guide
Understanding Firewalls
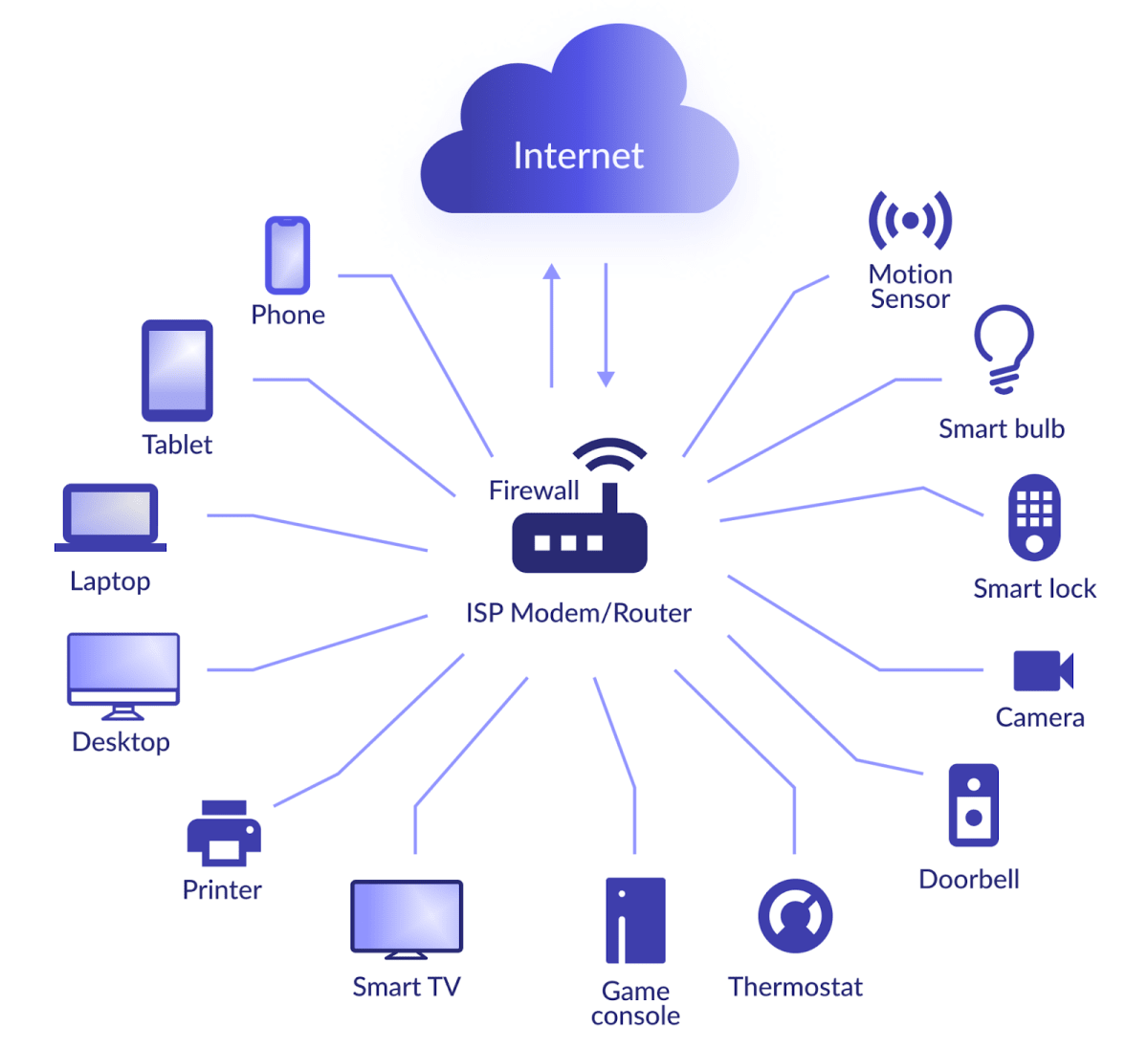
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between trusted and untrusted networks, such as the internet and your internal IoT network.
Types of Firewalls:
- Packet Filtering Firewalls
- Stateful Inspection Firewalls
- Application-Level Gateways (Proxy Firewalls)
- Next-Generation Firewalls
For IoT devices, a firewall can be configured to allow only necessary traffic while blocking potentially harmful connections. This ensures that your devices remain protected from malicious attacks.
Firewall Benefits for IoT
Implementing a firewall in your IoT network offers several advantages:
- Protection against unauthorized access
- Prevention of malware and virus propagation
- Enhanced privacy and data confidentiality
- Improved network performance through traffic filtering
By combining SSH and firewall technologies, you can create a robust security framework for your IoT devices.
Why Combine SSH and Firewalls for IoT Security?
Both SSH and firewalls play critical roles in securing IoT networks. SSH ensures secure communication between devices, while firewalls control access to the network. Together, they provide a comprehensive security solution that addresses multiple threat vectors.
Advantages of Combining SSH and Firewalls:
- Double-layered protection against attacks
- Secure remote access to IoT devices
- Granular control over network traffic
- Enhanced logging and monitoring capabilities
By integrating these technologies, you can minimize vulnerabilities and protect your IoT infrastructure from a wide range of cyber threats.
Preparation for SSH IoT Firewall Setup
Before setting up SSH and firewall for your IoT devices, it's essential to prepare your environment properly. This involves gathering necessary tools, configuring your devices, and planning your network architecture.
Preparation Steps:
- Identify all IoT devices in your network
- Ensure all devices are updated with the latest firmware
- Choose a reliable SSH client and firewall software
- Plan your network layout and security policies
Having a well-structured plan will help you avoid common pitfalls during the setup process and ensure a smooth implementation.
Choosing the Right Tools
Selecting the appropriate tools is crucial for successful SSH and firewall deployment. Consider factors such as ease of use, compatibility with your devices, and support for advanced security features.
Some popular SSH clients include:
- PuTTY
- OpenSSH
- SSH Secure Shell Client
For firewalls, options like:
- pfSense
- iptables
- Firewalld
offer robust security features tailored for IoT environments.
Installation of SSH and Firewall
Once your preparation is complete, the next step is to install SSH and firewall software on your IoT devices and network gateway. Follow these steps to ensure a successful installation:
SSH Installation:
- Download and install an SSH server on your IoT devices
- Configure the SSH server settings, such as port number and authentication methods
- Test the SSH connection to ensure proper functionality
Firewall Installation:
- Install the chosen firewall software on your network gateway
- Set up basic firewall rules to allow necessary traffic
- Verify that the firewall is functioning correctly
Proper installation is vital for ensuring that both SSH and firewall operate seamlessly in your IoT network.
Integration of SSH and Firewall
After installing both components, integrate them by configuring SSH to work within the firewall's security framework. This involves setting up rules that allow SSH traffic while blocking unauthorized access.
Integration Steps:
- Define firewall rules for SSH traffic
- Enable SSH tunneling through the firewall
- Monitor and adjust settings as needed
This integration ensures that your IoT devices are protected while maintaining secure communication channels.
Configuration of SSH and Firewall
Configuring SSH and firewall settings is a critical step in securing your IoT network. Proper configuration ensures that both technologies work harmoniously to protect your devices.
SSH Configuration:
- Set up strong password policies or use key-based authentication
- Disable root login to prevent unauthorized access
- Enable logging to track SSH activity
Firewall Configuration:
- Create rules to allow only necessary ports and IP addresses
- Implement intrusion detection and prevention systems
- Regularly update firewall rules to address new threats
Thorough configuration of both SSH and firewall settings is essential for maximizing their security capabilities.
Optimizing Performance
To ensure optimal performance of your SSH IoT firewall setup, consider the following tips:
- Monitor network traffic regularly
- Adjust firewall rules based on usage patterns
- Optimize SSH settings for faster connections
By fine-tuning your configuration, you can achieve a balance between security and performance in your IoT network.
Testing the SSH IoT Firewall
After completing the setup and configuration, it's crucial to test your SSH IoT firewall thoroughly. Testing ensures that everything is functioning as expected and identifies any potential issues before deployment.
Testing Steps:
- Attempt to access IoT devices using SSH from authorized and unauthorized IP addresses
- Check firewall logs for blocked and allowed connections
- Simulate various attack scenarios to test the system's resilience
Conducting comprehensive tests will help you verify the effectiveness of your SSH IoT firewall implementation.
Common Test Scenarios
Here are some common test scenarios to consider:
- Port scanning attacks
- Brute force login attempts
- Malware propagation through the network
By simulating these scenarios, you can evaluate how well your SSH IoT firewall handles real-world threats.
Advanced Security Measures
For enhanced security, consider implementing advanced measures alongside your SSH IoT firewall setup. These measures provide an additional layer of protection against sophisticated cyber threats.
Advanced Security Techniques:
- Implement two-factor authentication for SSH access
- Use intrusion detection systems (IDS) to monitor for suspicious activity
- Regularly audit and update security policies
By adopting these advanced techniques, you can further strengthen the security of your IoT network.
Encryption and Data Protection
Encrypting data both in transit and at rest is crucial for safeguarding sensitive information. Use strong encryption algorithms and protocols to protect your data from unauthorized access.
Encryption Recommendations:
- Use AES-256 for data encryption
- Enable SSL/TLS for secure web communications
- Regularly rotate encryption keys
Implementing robust encryption practices will help ensure the confidentiality and integrity of your IoT data.
Troubleshooting Common Issues
Despite careful planning and implementation, issues may arise during the operation of your SSH IoT firewall. Here are some common problems and their solutions:
Common Issues:
- SSH connection failures
- Firewall blocking legitimate traffic
- Performance degradation
Solutions:
- Check SSH server settings and ensure proper configuration
- Review firewall rules and adjust as needed
- Optimize network settings to improve performance
Addressing these issues promptly will help maintain the stability and security of your IoT network.
Diagnostic Tools
Using diagnostic tools can aid in identifying and resolving problems quickly. Some useful tools include:
- netstat for analyzing network connections
- tcpdump for capturing and analyzing network traffic
- ping and traceroute for troubleshooting connectivity issues
These tools provide valuable insights into your network's performance and security status.
Best Practices for SSH IoT Firewall
To maximize the effectiveness of your SSH IoT firewall setup, follow these best practices:
Best Practices:
- Regularly update firmware and software on all devices
- Keep SSH and firewall configurations up-to-date
- Monitor network activity continuously
- Conduct regular security audits