Mastering IoT Device SSH On AWS: A Comprehensive Guide
IoT device SSH AWS has become an essential practice for modern businesses aiming to secure their internet-connected devices while leveraging cloud computing capabilities. As the Internet of Things (IoT) continues to expand, integrating IoT devices with secure shell (SSH) protocols on Amazon Web Services (AWS) provides a robust solution for remote management and enhanced security. In this article, we will explore everything you need to know about configuring and managing IoT devices with SSH on AWS, ensuring optimal performance and protection.
The integration of IoT devices into cloud environments like AWS has revolutionized how organizations handle data collection, storage, and analysis. However, with the rise in connectivity comes the need for stronger security measures. SSH serves as a critical tool for securing communication between IoT devices and cloud servers. Understanding how to implement this effectively can significantly enhance your IoT infrastructure.
This guide will delve into the technical aspects of IoT device SSH AWS, covering everything from basic configurations to advanced security practices. Whether you're a beginner exploring IoT and cloud computing or an experienced professional seeking to refine your skills, this article offers valuable insights and actionable advice. Let's dive in!
Read also:Unveiling The Remarkable Journey Of Roberta Gonzales
Table of Contents
- Introduction to IoT Device SSH AWS
- Why Choose AWS for IoT Devices
- Setting Up SSH for IoT Devices
- Configuring AWS Security for IoT SSH
- Best Practices for IoT Device SSH AWS
- Troubleshooting Common Issues
- Scaling IoT Device SSH AWS
- Data Privacy and Compliance
- Real-World Applications of IoT Device SSH AWS
- Future Trends in IoT Device SSH AWS
- Conclusion and Next Steps
Introduction to IoT Device SSH AWS
The Internet of Things (IoT) has transformed the way devices communicate and interact with each other. IoT devices, ranging from smart home appliances to industrial sensors, generate vast amounts of data that require secure and efficient handling. AWS provides a powerful platform for managing IoT devices, and integrating SSH into this ecosystem ensures secure communication.
SSH, or Secure Shell, is a cryptographic protocol used to securely access and manage remote devices. By leveraging SSH on AWS, organizations can ensure that their IoT devices are protected from unauthorized access and potential cyber threats. This section will explore the fundamentals of IoT device SSH AWS and its significance in today's digital landscape.
Key benefits of using SSH for IoT devices on AWS include enhanced security, streamlined remote management, and seamless integration with existing cloud infrastructure. As organizations increasingly rely on IoT for critical operations, understanding how to implement SSH effectively is crucial for maintaining operational integrity.
Why Choose AWS for IoT Devices
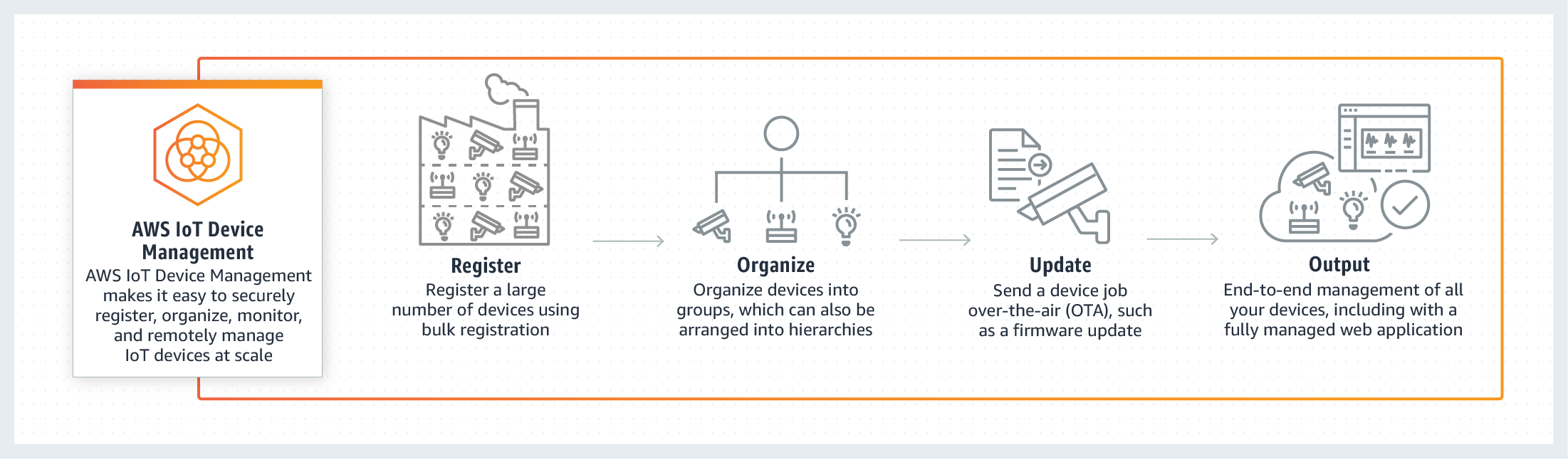
AWS offers a comprehensive suite of services tailored for IoT applications, making it a preferred choice for businesses of all sizes. The platform provides robust tools for device management, data analytics, and secure communication, ensuring that IoT deployments are both scalable and secure.
Advantages of AWS for IoT Devices
- Scalability: AWS allows you to scale your IoT infrastructure based on demand, accommodating growth without compromising performance.
- Security: With advanced security features, including encryption and access controls, AWS ensures that your IoT devices and data remain protected.
- Integration: AWS seamlessly integrates with third-party applications and services, enabling a unified ecosystem for IoT management.
According to a report by Gartner, AWS holds a significant share of the cloud computing market, driven by its extensive range of services and global infrastructure. This makes it an ideal platform for deploying and managing IoT devices with SSH.
Setting Up SSH for IoT Devices
Configuring SSH for IoT devices involves several steps, from generating SSH keys to establishing secure connections. This section will walk you through the process, ensuring that your IoT devices are securely integrated with AWS.
Read also:Olivia Beavers Husband A Comprehensive Look Into Her Personal Life
Step-by-Step Guide
- Generate SSH Keys: Use tools like OpenSSH to create public and private key pairs for secure authentication.
- Install SSH Client: Ensure that your IoT devices have an SSH client installed and configured.
- Set Up AWS EC2 Instances: Launch EC2 instances on AWS to serve as secure endpoints for your IoT devices.
- Configure Security Groups: Define security groups to restrict access to your IoT devices and EC2 instances.
Proper configuration of SSH ensures that only authorized users and devices can access your IoT infrastructure, minimizing the risk of unauthorized access.
Configuring AWS Security for IoT SSH
Security is paramount when managing IoT devices on AWS. Implementing robust security measures is essential to protect sensitive data and prevent potential breaches. This section will explore best practices for securing IoT device SSH AWS.
Key Security Measures
- Use IAM Roles: Leverage AWS Identity and Access Management (IAM) to define roles and permissions for IoT devices and users.
- Enable Encryption: Use AWS Key Management Service (KMS) to encrypt data transmitted between IoT devices and cloud servers.
- Monitor Activity: Utilize AWS CloudTrail to monitor and audit SSH activity, ensuring compliance with security policies.
By adhering to these security practices, organizations can create a secure environment for their IoT devices, reducing the risk of data breaches and unauthorized access.
Best Practices for IoT Device SSH AWS
Adopting best practices is essential for optimizing the performance and security of IoT device SSH AWS. This section will provide actionable tips to enhance your IoT infrastructure.
Implementing Best Practices
- Regular Updates: Keep your IoT devices and SSH software up to date with the latest security patches and updates.
- Limit Access: Restrict SSH access to only necessary users and devices, reducing the attack surface.
- Monitor Logs: Analyze SSH logs regularly to detect and respond to suspicious activities promptly.
Following these best practices ensures that your IoT devices remain secure and perform optimally, even as your infrastructure scales.
Troubleshooting Common Issues
Despite careful configuration, issues may arise when managing IoT devices with SSH on AWS. This section will address common challenges and provide solutions to resolve them.
Common Issues and Solutions
- Connection Errors: Verify SSH keys and security group settings to resolve connection issues.
- Performance Bottlenecks: Optimize EC2 instance types and configurations to improve performance.
- Security Breaches: Conduct regular security audits and update security policies to mitigate breaches.
By identifying and addressing these issues promptly, organizations can maintain a stable and secure IoT infrastructure.
Scaling IoT Device SSH AWS
As IoT deployments grow, scaling becomes a critical consideration. AWS provides tools and services to help organizations scale their IoT infrastructure efficiently. This section will explore strategies for scaling IoT device SSH AWS.
Scaling Strategies
- Auto Scaling: Use AWS Auto Scaling to automatically adjust resources based on demand.
- Load Balancing: Implement load balancers to distribute traffic across multiple IoT devices and EC2 instances.
- Database Optimization: Optimize database configurations to handle increased data loads effectively.
Effective scaling ensures that your IoT infrastructure can handle growth without compromising performance or security.
Data Privacy and Compliance
Data privacy and compliance are critical considerations when managing IoT devices on AWS. Organizations must adhere to regulations such as GDPR and HIPAA to protect sensitive information. This section will discuss how to ensure compliance with these regulations.
Ensuring Compliance
- Data Encryption: Encrypt data at rest and in transit to meet privacy requirements.
- Access Controls: Implement strict access controls to limit data exposure.
- Regular Audits: Conduct regular audits to ensure compliance with relevant regulations.
By prioritizing data privacy and compliance, organizations can build trust with their customers and avoid potential legal issues.
Real-World Applications of IoT Device SSH AWS
IoT device SSH AWS has been successfully implemented in various industries, ranging from healthcare to manufacturing. This section will explore real-world applications and success stories.
Industry Applications
- Healthcare: Securely manage medical devices and patient data using SSH on AWS.
- Manufacturing: Monitor and control industrial equipment remotely with IoT devices and SSH.
- Retail: Enhance inventory management and customer experience through IoT-enabled systems.
These applications demonstrate the versatility and effectiveness of IoT device SSH AWS in addressing industry-specific challenges.
Future Trends in IoT Device SSH AWS
The future of IoT device SSH AWS looks promising, with advancements in technology driving innovation. This section will highlight emerging trends and their potential impact on the IoT landscape.
Emerging Trends
- Edge Computing: Integrating edge computing with IoT devices to enhance processing capabilities.
- Artificial Intelligence: Leveraging AI for predictive maintenance and improved decision-making.
- Quantum Computing: Exploring the potential of quantum computing in securing IoT communications.
Staying informed about these trends will help organizations prepare for the future of IoT and cloud computing.
Conclusion and Next Steps
In conclusion, IoT device SSH AWS offers a powerful solution for managing and securing IoT devices in today's interconnected world. By following the guidelines and best practices outlined in this article, organizations can optimize their IoT infrastructure for performance, security, and scalability.
We encourage readers to take the following steps:
- Experiment with SSH configurations on AWS to familiarize yourself with the process.
- Stay updated with the latest trends and advancements in IoT and cloud computing.
- Share your experiences and insights in the comments section below.
Thank you for reading, and we look forward to seeing how you apply these concepts to enhance your IoT deployments. For more articles on IoT and cloud computing, explore our website and stay connected!