Mastering IoT Remote Access With SSH On AWS: A Comprehensive Guide
IoT remote access via SSH on AWS has become a cornerstone for modern technology solutions, enabling seamless connectivity and secure communication between devices. The Internet of Things (IoT) continues to revolutionize industries by connecting devices and allowing them to exchange data. However, ensuring secure and reliable remote access to these devices is critical. This is where Secure Shell (SSH) on Amazon Web Services (AWS) plays a pivotal role. By leveraging AWS's robust infrastructure, organizations can securely manage IoT devices from anywhere in the world.
As IoT adoption grows, so does the demand for secure and scalable remote access solutions. SSH, a widely-used protocol, provides encrypted communication channels, ensuring that data transmitted between devices remains protected. When combined with AWS, this setup not only enhances security but also offers unparalleled scalability and flexibility for IoT deployments.
This article will explore the intricacies of IoT remote access using SSH on AWS. From setting up the environment to troubleshooting common issues, we aim to provide a comprehensive guide that caters to both beginners and advanced users. By the end of this article, you'll have a clear understanding of how to implement and manage IoT devices through SSH on AWS effectively.
Read also:Unveiling The World Of Movierulz Hd Bar Your Ultimate Guide
Table of Contents
- Introduction to IoT Remote Access
- Understanding SSH Basics
- AWS Overview for IoT
- Setting Up IoT Remote Access with SSH on AWS
- Enhancing Security Measures
- Scaling IoT Deployments on AWS
- Troubleshooting Common Issues
- Real-World Use Cases
- Best Practices for IoT Remote Access
- The Future of IoT Remote Access
- Conclusion
Introduction to IoT Remote Access
What is IoT Remote Access?
IoT remote access refers to the ability to connect to and manage IoT devices from a remote location. This capability is essential for maintaining and troubleshooting devices without requiring physical presence. For businesses, this translates into cost savings and improved operational efficiency.
Why Use SSH for IoT Remote Access?
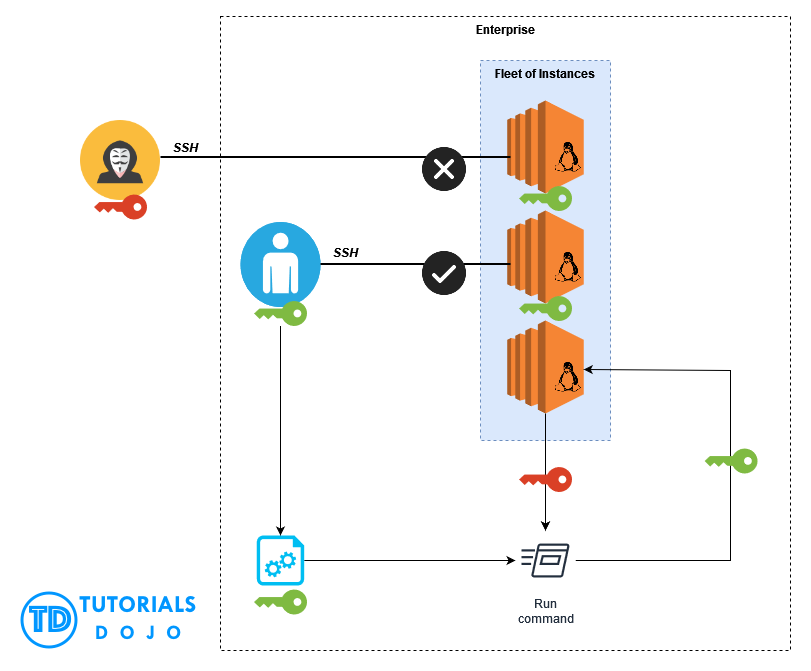
SSH is a secure protocol that encrypts data transmitted between devices, making it an ideal choice for IoT remote access. By using SSH, organizations can ensure that sensitive information remains protected from unauthorized access and cyber threats.
The Role of AWS in IoT Remote Access
AWS provides a scalable and reliable infrastructure for IoT deployments. With features like AWS IoT Core and EC2 instances, managing IoT devices becomes easier and more efficient. AWS also offers robust security features, ensuring that IoT remote access remains secure and compliant with industry standards.
Understanding SSH Basics
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It is widely used for remote command-line login and data transfer.
How Does SSH Work?
SSH establishes a secure connection by using encryption algorithms to protect data in transit. It also supports authentication methods such as passwords and public-key cryptography, ensuring that only authorized users can access the system.
Benefits of Using SSH
- Enhanced security through encryption
- Reliable authentication mechanisms
- Support for multiple protocols and applications
- Wide adoption and compatibility with various platforms
AWS Overview for IoT
What is AWS IoT Core?
AWS IoT Core is a managed cloud service that allows connected devices to interact with cloud applications and other devices securely. It supports billions of devices and trillions of messages, making it suitable for large-scale IoT deployments.
Read also:Tom Hanks Accusations The Truth Behind The Allegations
Key Features of AWS IoT Core
- Device Management: Register, monitor, and update IoT devices
- Message Routing: Efficiently route messages between devices and applications
- Security: Implement end-to-end encryption and authentication
- Scalability: Handle massive amounts of data and devices
Integrating AWS IoT Core with SSH
By combining AWS IoT Core with SSH, organizations can create a secure and scalable environment for IoT remote access. This integration enables seamless communication between devices while maintaining high levels of security.
Setting Up IoT Remote Access with SSH on AWS
Prerequisites
Before setting up IoT remote access with SSH on AWS, ensure you have the following:
- An AWS account
- An IoT device with SSH capabilities
- A public IP address or domain name
- Basic knowledge of AWS services and SSH
Step-by-Step Guide
Follow these steps to set up IoT remote access with SSH on AWS:
- Create an EC2 instance on AWS and configure it to act as a SSH server.
- Install the necessary software on your IoT device to enable SSH connectivity.
- Configure security groups and firewall settings to allow SSH traffic.
- Test the connection by accessing your IoT device remotely using SSH.
Tips for Successful Setup
- Use strong passwords and enable two-factor authentication for added security.
- Regularly update your software and firmware to protect against vulnerabilities.
- Monitor system logs to detect and respond to potential security threats.
Enhancing Security Measures
Best Security Practices for IoT Remote Access
Implementing robust security measures is crucial for protecting IoT devices and data. Consider the following practices:
- Use public-key authentication instead of passwords for SSH.
- Restrict SSH access to specific IP addresses or ranges.
- Enable logging and monitoring to track unauthorized access attempts.
Common Security Threats and How to Mitigate Them
IoT devices are vulnerable to various security threats, including:
- Brute-force attacks: Use fail2ban or similar tools to block repeated login attempts.
- Man-in-the-middle attacks: Ensure that all communications are encrypted using SSH.
- Malware infections: Regularly scan devices for malware and keep them updated.
Compliance with Industry Standards
When implementing IoT remote access with SSH on AWS, ensure compliance with relevant industry standards such as:
- ISO/IEC 27001: Information Security Management
- NIST Cybersecurity Framework
- GDPR: General Data Protection Regulation
Scaling IoT Deployments on AWS
Challenges of Scaling IoT Deployments
As IoT deployments grow, managing and securing devices becomes increasingly complex. Common challenges include:
- Handling large volumes of data and devices
- Ensuring consistent performance and reliability
- Maintaining security and compliance
Solutions for Scalability
AWS offers several solutions to address scalability challenges, including:
- AWS IoT Device Management: Simplifies device registration and monitoring.
- AWS Lambda: Enables serverless computing for processing IoT data.
- Amazon S3: Provides scalable storage for IoT data.
Best Practices for Scalable IoT Deployments
- Design your architecture with scalability in mind from the beginning.
- Use automation tools to streamline device management and maintenance.
- Monitor system performance and adjust resources as needed.
Troubleshooting Common Issues
Identifying and Resolving SSH Connection Problems
Common SSH connection issues include:
- Incorrect username or password
- Firewall or security group restrictions
- Network connectivity problems
Resolving these issues typically involves checking configuration settings, verifying network connectivity, and reviewing logs for error messages.
Debugging IoT Device Issues
When troubleshooting IoT devices, consider the following steps:
- Check device firmware and software for updates.
- Verify device connectivity and network settings.
- Examine system logs for error messages or warnings.
Seeking Support from AWS
AWS provides extensive support resources, including documentation, forums, and customer support. Leverage these resources to resolve issues quickly and efficiently.
Real-World Use Cases
Industrial IoT Applications
In industrial settings, IoT remote access with SSH on AWS enables engineers to monitor and manage equipment from remote locations. This capability improves maintenance efficiency and reduces downtime.
Smart Home Solutions
For smart home applications, IoT remote access allows users to control and manage devices such as thermostats, security cameras, and lighting systems from anywhere in the world.
Healthcare IoT Deployments
In healthcare, IoT remote access facilitates the monitoring of medical devices and patient data, ensuring timely interventions and improved patient care.
Best Practices for IoT Remote Access
Planning and Design
Start by defining clear objectives and requirements for your IoT deployment. Consider factors such as device types, data volumes, and security needs when designing your architecture.
Implementation and Testing
Thoroughly test your setup before deploying it in a production environment. This includes verifying connectivity, security, and scalability under various conditions.
Maintenance and Monitoring
Regularly maintain and monitor your IoT devices and systems to ensure optimal performance and security. Implement automated tools to streamline these processes and reduce manual intervention.
The Future of IoT Remote Access
Emerging Trends in IoT
The future of IoT remote access is shaped by emerging trends such as:
- 5G networks: Enabling faster and more reliable connectivity.
- Edge computing: Processing data closer to the source for reduced latency.
- AI and machine learning: Enhancing device intelligence and automation.
Impact of AWS Innovations
AWS continues to innovate in the IoT space, introducing new services and features that enhance scalability, security, and usability. These advancements will play a significant role in shaping the future of IoT remote access.
Preparation for the Future
To prepare for the future of IoT remote access, organizations should:
- Stay informed about emerging technologies and trends.
- Invest in training and development for staff.
- Adopt flexible and scalable architectures to accommodate growth.
Conclusion
IoT remote access with SSH on AWS offers a secure and scalable solution for managing IoT devices. By following the guidelines and best practices outlined in this article, organizations can effectively implement and maintain IoT deployments that meet their business needs.
We encourage readers to share their experiences and insights in the comments section below. Additionally, explore other articles on our site to learn more about IoT, AWS, and related technologies. Together, we can shape the future of IoT remote access and drive innovation in this exciting field.