Mastering IoT SSH Access On AWS: A Comprehensive Guide
In today's interconnected world, IoT SSH access on AWS plays a crucial role in ensuring secure communication between devices and cloud infrastructure. As more organizations embrace IoT solutions, the demand for robust security protocols has never been higher. This article delves into the nuances of securing IoT devices using SSH access on AWS, providing actionable insights and best practices.
The Internet of Things (IoT) continues to revolutionize industries by enabling seamless communication between devices. However, with this increased connectivity comes the challenge of maintaining security. AWS offers a powerful platform for managing IoT devices, and leveraging SSH access is one of the most effective ways to enhance security.
This guide aims to provide a comprehensive understanding of IoT SSH access on AWS, covering everything from basic setup to advanced configurations. Whether you're a beginner or an experienced professional, this article will equip you with the knowledge needed to secure your IoT infrastructure effectively.
Read also:Delores Nowzaradan The Woman Behind The Iconic Legal Cases
Table of Contents
- Introduction to IoT SSH on AWS
- Benefits of Using SSH for IoT
- Setting Up SSH Access on AWS
- Securing IoT Devices with SSH
- Best Practices for IoT SSH Access
- Common SSH Issues and Resolutions
- Optimizing IoT SSH Performance
- Integrating SSH with AWS Services
- Cost Management for IoT SSH on AWS
- Future Trends in IoT SSH Access
- Conclusion
Introduction to IoT SSH on AWS
IoT SSH access on AWS represents a cutting-edge approach to securing device communication. By leveraging the Secure Shell (SSH) protocol, organizations can establish encrypted connections between IoT devices and cloud-based resources. AWS provides a scalable and reliable infrastructure to support these operations, making it an ideal choice for enterprises of all sizes.
The integration of SSH within the AWS ecosystem ensures that sensitive data remains protected during transit. This is particularly important in industries such as healthcare, finance, and manufacturing, where data security is paramount. Understanding the fundamentals of IoT SSH access on AWS is the first step toward implementing a secure and efficient IoT infrastructure.
Benefits of Using SSH for IoT
Using SSH for IoT offers numerous advantages that contribute to enhanced security and operational efficiency. Below are some of the key benefits:
- Encryption: SSH encrypts all data transmitted between devices and servers, preventing unauthorized access.
- Authentication: The protocol supports strong authentication mechanisms, ensuring that only authorized users can access IoT devices.
- Reliability: SSH connections are robust and can withstand network interruptions, providing stable communication.
- Scalability: AWS's infrastructure allows for seamless scaling of SSH-enabled IoT deployments, accommodating growing demands.
Setting Up SSH Access on AWS
Creating an EC2 Instance
To begin using SSH for IoT on AWS, you first need to create an EC2 instance. This virtual server will act as the central hub for managing IoT devices. Follow these steps to set up your instance:
- Log in to your AWS Management Console and navigate to the EC2 Dashboard.
- Click on "Launch Instance" and select an Amazon Machine Image (AMI) suitable for your IoT application.
- Configure the instance details, including instance type, storage, and networking settings.
- Create a new key pair or use an existing one to securely access your instance via SSH.
Configuring Security Groups
Security groups act as virtual firewalls for your EC2 instances. Proper configuration is essential to allow SSH access while maintaining security:
- In the EC2 Dashboard, select "Security Groups" from the sidebar.
- Create a new security group and define rules to permit SSH traffic (port 22) from trusted IP addresses.
- Associate the security group with your EC2 instance to enforce the defined rules.
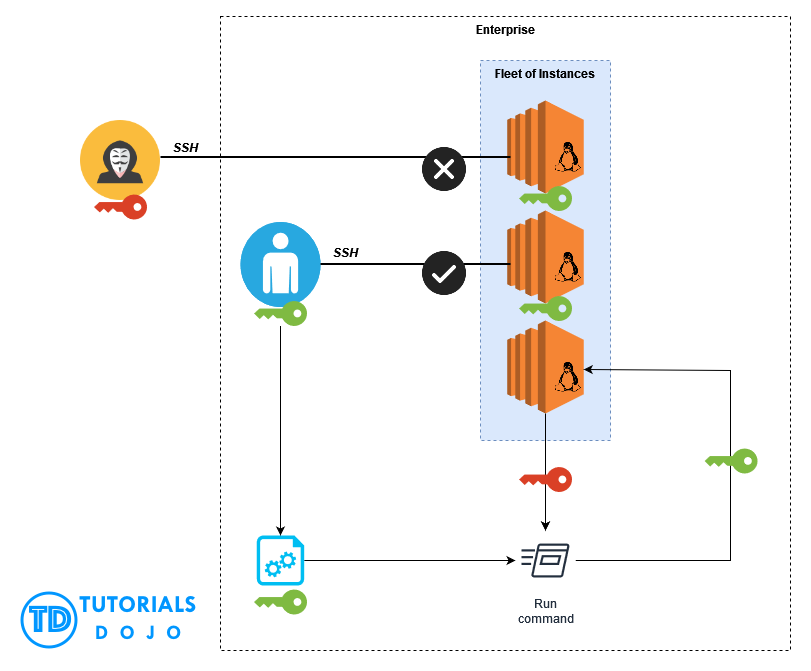
Securing IoT Devices with SSH
Once your EC2 instance is set up, the next step is to secure your IoT devices using SSH. This involves configuring SSH settings on both the server and device ends. Key considerations include:
Read also:Aaron Carter And Diddy The Untold Story Of Their Connection
- Disabling password-based authentication in favor of public key authentication.
- Implementing SSH key rotation policies to minimize the risk of compromised keys.
- Monitoring SSH login attempts for suspicious activities and setting up alerts for unauthorized access.
Best Practices for IoT SSH Access
Adhering to best practices ensures that your IoT SSH setup remains secure and efficient. Some recommendations include:
- Regularly updating SSH software and libraries to patch vulnerabilities.
- Limiting SSH access to specific IP addresses or subnets.
- Using strong, unique passwords for user accounts and enabling multi-factor authentication (MFA).
- Logging SSH activities and reviewing logs periodically to detect potential threats.
Common SSH Issues and Resolutions
Despite its robustness, SSH can sometimes encounter issues. Below are some common problems and their solutions:
- Connection Refused: Ensure that the security group allows SSH traffic and that the instance is running.
- Permission Denied (Public Key): Verify that the correct SSH key is being used and that the key permissions are set correctly.
- Timeout Errors: Check network connectivity and ensure that the instance's public IP address is accessible.
Optimizing IoT SSH Performance
Optimizing SSH performance is crucial for maintaining efficient IoT operations. Techniques such as compression, increasing buffer sizes, and using faster encryption algorithms can significantly improve connection speeds. Additionally, consider implementing load balancing to distribute SSH traffic across multiple instances, ensuring high availability and reduced latency.
Integrating SSH with AWS Services
AWS provides various services that can enhance SSH functionality for IoT applications. For instance, AWS Systems Manager allows for remote management of EC2 instances without requiring SSH access. Similarly, AWS IoT Core can be integrated with SSH to streamline device communication and management. Exploring these integrations can unlock new possibilities for optimizing your IoT infrastructure.
Cost Management for IoT SSH on AWS
Managing costs is an essential aspect of deploying IoT SSH on AWS. To keep expenses under control, consider the following strategies:
- Utilize AWS's pricing calculator to estimate costs before deploying resources.
- Opt for Reserved Instances or Spot Instances when applicable to reduce expenses.
- Monitor usage metrics and adjust resource allocation based on demand fluctuations.
Future Trends in IoT SSH Access
The landscape of IoT SSH access on AWS is continually evolving. Emerging trends such as quantum-resistant encryption, AI-driven threat detection, and decentralized architectures promise to enhance security and scalability. Staying informed about these developments will help organizations future-proof their IoT deployments and remain competitive in the digital age.
Conclusion
In conclusion, IoT SSH access on AWS offers a secure and efficient solution for managing IoT devices. By following the guidelines and best practices outlined in this article, you can effectively implement SSH in your IoT infrastructure and protect sensitive data. We encourage readers to share their thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into AWS and IoT technologies.
Don't forget to bookmark this page for future reference and subscribe to our newsletter for updates on the latest trends in IoT and cloud computing. Together, let's build a more connected and secure world!