Mastering IoT SSH Over SSH On AWS: A Comprehensive Guide
In today's rapidly evolving technological landscape, IoT SSH over SSH on AWS has become a critical concept for businesses looking to enhance their cybersecurity measures while managing IoT devices efficiently. The integration of IoT devices into cloud-based systems has brought about new challenges, particularly in ensuring secure communication and data transfer. Understanding how to use SSH tunnels within an AWS environment can significantly strengthen your network's security and protect sensitive information.
This article will delve into the intricacies of IoT SSH over SSH on AWS, providing a detailed exploration of its applications, benefits, and implementation strategies. Whether you're a seasoned IT professional or a beginner exploring cloud security, this guide will equip you with the knowledge needed to leverage SSH effectively for IoT device management.
By the end of this article, you will have a comprehensive understanding of how to set up secure IoT communication using SSH tunnels on AWS, the importance of cybersecurity in IoT ecosystems, and actionable steps to protect your infrastructure. Let's dive in!
Read also:Hikaru Nagi Bio A Comprehensive Look Into The Life Of A Rising Star
Table of Contents
- Introduction to IoT SSH Over SSH on AWS
- Understanding the Basics of IoT and SSH
- Role of AWS in IoT SSH Over SSH
- Setting Up IoT SSH Over SSH on AWS
- Security Considerations in IoT SSH Over SSH
- Benefits of Using IoT SSH Over SSH on AWS
- Common Challenges and Solutions
- Best Practices for IoT SSH Over SSH on AWS
- The Future of IoT SSH Over SSH on AWS
- Conclusion and Next Steps
Introduction to IoT SSH Over SSH on AWS
What is IoT SSH Over SSH?
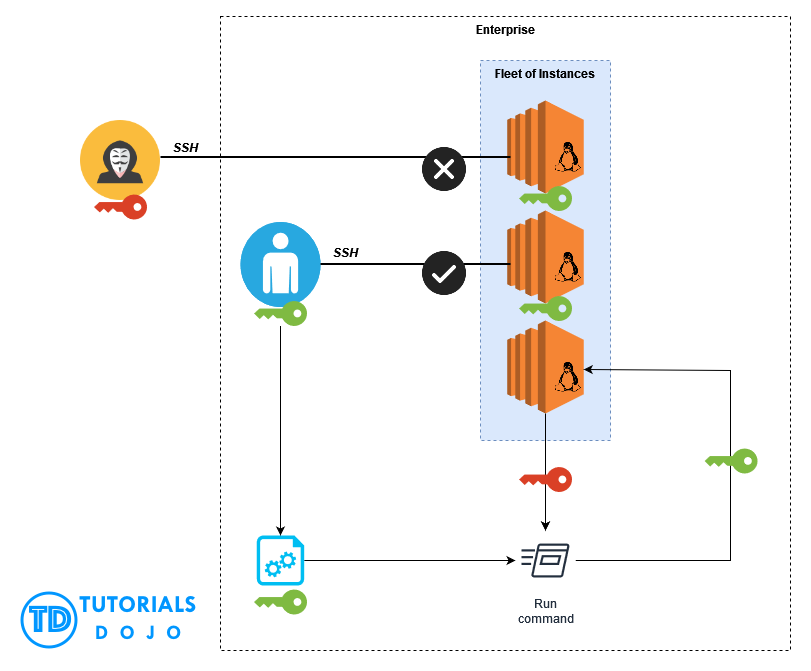
IoT SSH over SSH refers to the practice of tunneling Secure Shell (SSH) connections through another SSH connection to securely manage IoT devices within a cloud environment. This technique is particularly useful for creating secure communication channels between IoT devices and servers hosted on platforms like AWS.
By leveraging SSH tunnels, organizations can protect sensitive data transmitted between IoT devices and cloud servers from unauthorized access and potential cyber threats. This method ensures that all communication remains encrypted and secure, even when traversing public networks.
Why Use AWS for IoT SSH?
AWS provides a robust and scalable infrastructure for managing IoT devices and implementing SSH tunnels. With its advanced security features and global network of data centers, AWS offers an ideal platform for deploying IoT SSH solutions. The platform's support for various protocols and integration with other AWS services makes it a top choice for organizations looking to enhance their IoT security.
Understanding the Basics of IoT and SSH
What is IoT?
The Internet of Things (IoT) refers to the network of interconnected devices capable of collecting and exchanging data. These devices range from simple sensors to complex machines, all designed to enhance automation and improve efficiency in various industries. IoT has revolutionized the way businesses operate by enabling real-time monitoring, predictive maintenance, and data-driven decision-making.
What is SSH?
Secure Shell (SSH) is a cryptographic network protocol used to secure communication between devices over an unsecured network. It provides a secure channel for remote access, file transfer, and command execution. SSH is widely used in IT infrastructure for its strong encryption capabilities and ability to protect sensitive data during transmission.
Role of AWS in IoT SSH Over SSH
AWS plays a pivotal role in facilitating IoT SSH over SSH by offering a comprehensive suite of services designed to enhance security and scalability. AWS IoT Core, for instance, allows developers to connect IoT devices easily and securely, while AWS Lambda enables the execution of code in response to events without managing servers. These services, combined with AWS's robust security features, make it an ideal platform for implementing IoT SSH solutions.
Read also:Kikaru Nagi The Rising Star In The World Of Anime And Manga
Setting Up IoT SSH Over SSH on AWS
Step-by-Step Guide
Setting up IoT SSH over SSH on AWS involves several key steps, including configuring SSH tunnels, deploying IoT devices, and integrating with AWS services. Below is a detailed guide to help you get started:
- Install and configure SSH clients and servers on your IoT devices and AWS instances.
- Create an SSH tunnel to establish a secure connection between your local machine and the AWS server.
- Deploy IoT devices using AWS IoT Core and ensure they are properly registered and authenticated.
- Implement security measures, such as using strong passwords and enabling two-factor authentication.
- Monitor and manage your IoT devices using AWS CloudWatch and other monitoring tools.
Security Considerations in IoT SSH Over SSH
Key Security Measures
When implementing IoT SSH over SSH on AWS, it is crucial to prioritize security to protect sensitive data and prevent unauthorized access. Here are some key security measures to consider:
- Use strong encryption protocols, such as AES-256, to secure data transmission.
- Implement role-based access control (RBAC) to restrict access to sensitive resources.
- Regularly update and patch your IoT devices and AWS instances to address security vulnerabilities.
- Enable logging and monitoring to detect and respond to suspicious activities promptly.
Benefits of Using IoT SSH Over SSH on AWS
Using IoT SSH over SSH on AWS offers numerous benefits, including enhanced security, improved scalability, and greater flexibility in managing IoT devices. By leveraging AWS's advanced features and services, organizations can optimize their IoT infrastructure and ensure seamless communication between devices and servers.
Common Challenges and Solutions
Addressing Common Challenges
While implementing IoT SSH over SSH on AWS, organizations may encounter several challenges, such as managing large-scale deployments, ensuring compatibility with diverse devices, and maintaining high availability. Below are some solutions to these challenges:
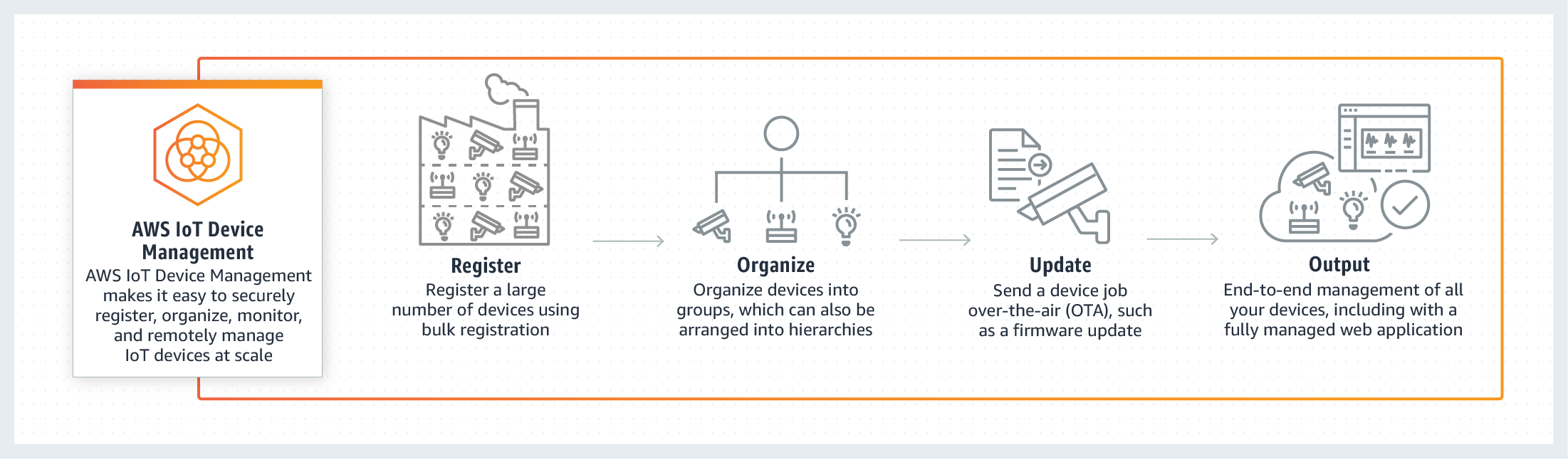
- Utilize AWS IoT Device Management to simplify the provisioning and monitoring of IoT devices.
- Adopt a standardized approach to device communication and data exchange to ensure compatibility.
- Implement redundancy and failover mechanisms to maintain high availability and reliability.
Best Practices for IoT SSH Over SSH on AWS
Adopting Best Practices
To maximize the effectiveness of IoT SSH over SSH on AWS, it is essential to follow best practices. These include:
- Regularly audit and review your security policies and procedures.
- Train your staff on cybersecurity best practices and the proper use of SSH tunnels.
- Document your configurations and processes to ensure consistency and ease of maintenance.
The Future of IoT SSH Over SSH on AWS
The future of IoT SSH over SSH on AWS looks promising, with advancements in technology and increasing adoption of IoT devices. As organizations continue to embrace cloud-based solutions, the demand for secure and scalable IoT management platforms will only grow. AWS is well-positioned to meet this demand, offering innovative solutions and cutting-edge technologies to support the evolving needs of businesses.
Conclusion and Next Steps
In conclusion, mastering IoT SSH over SSH on AWS is essential for organizations looking to enhance their cybersecurity measures and manage IoT devices effectively. By understanding the basics of IoT and SSH, leveraging AWS's robust infrastructure, and following best practices, you can create a secure and efficient IoT ecosystem.
We encourage you to take the next step by exploring AWS's extensive documentation and resources to deepen your knowledge of IoT SSH over SSH. Don't forget to leave a comment or share this article with your network to help others learn about this critical topic. Together, let's build a safer and more connected world!
References:
- AWS IoT Documentation: https://docs.aws.amazon.com/iot
- SSH Protocol Overview: https://www.ssh.com/ssh/protocol
- Cybersecurity Best Practices: https://www.cisa.gov/cybersecurity-best-practices