Mastering RemoteIoT Platform SSH Key For Raspberry Pi: A Comprehensive Guide
In today's digital age, the RemoteIoT platform has become an essential tool for managing IoT devices remotely. As more organizations and individuals embrace IoT technology, understanding how to secure your devices using SSH keys on Raspberry Pi is crucial. This guide will walk you through the process of setting up and managing SSH keys on Raspberry Pi, ensuring your IoT devices remain secure and accessible.
With the increasing demand for remote access to IoT devices, the importance of security cannot be overstated. SSH keys provide a robust layer of protection, making it difficult for unauthorized users to gain access to your devices. By following the steps outlined in this article, you can enhance the security of your Raspberry Pi and ensure seamless connectivity.
This article is designed to provide a detailed, step-by-step guide to setting up SSH keys on the RemoteIoT platform using Raspberry Pi. Whether you're a beginner or an experienced user, this guide will help you understand the intricacies of SSH keys and their role in securing your IoT devices.
Read also:Did Duane Lee Chapman Jr Attend Beths Funeral Exploring The Truth Behind The Headlines
Table of Contents
- Introduction to RemoteIoT Platform
- Understanding SSH Keys
- Raspberry Pi Overview
- Setting Up SSH Keys
- Securing Your RemoteIoT Platform
- Troubleshooting Common Issues
- Best Practices for SSH Keys
- Case Studies
- Future Trends in IoT Security
- Conclusion
Introduction to RemoteIoT Platform
The RemoteIoT platform is a powerful tool designed to facilitate the management of IoT devices remotely. It provides users with the ability to monitor, control, and secure their IoT devices from anywhere in the world. By leveraging advanced technologies such as SSH keys, the platform ensures that your devices remain protected against unauthorized access.
One of the key features of the RemoteIoT platform is its compatibility with Raspberry Pi, a versatile and affordable single-board computer. This combination allows users to create cost-effective IoT solutions without compromising on security or functionality.
Understanding SSH Keys
SSH keys are cryptographic keys used to authenticate users and devices in a secure manner. Unlike traditional password-based authentication, SSH keys provide a higher level of security by eliminating the risk of brute-force attacks. They consist of a public key and a private key, which work together to establish a secure connection.
When setting up SSH keys for Raspberry Pi, it's important to understand the role of each key:
- Public Key: This key is shared with the server (in this case, the Raspberry Pi) and is used to encrypt data.
- Private Key: This key must be kept secure and is used to decrypt data sent by the server.
Raspberry Pi Overview
Raspberry Pi is a series of small single-board computers developed by the Raspberry Pi Foundation. Known for its affordability and versatility, Raspberry Pi has become a popular choice for IoT projects. With its ability to run a variety of operating systems, including Linux, Raspberry Pi provides a robust platform for developing and deploying IoT applications.
In the context of the RemoteIoT platform, Raspberry Pi serves as the backbone of the system, enabling users to manage their IoT devices remotely. By securing Raspberry Pi with SSH keys, users can ensure that their devices remain protected against unauthorized access.
Read also:Katy Perry Before Fame The Untold Journey To Stardom
Setting Up SSH Keys
Setting up SSH keys for Raspberry Pi involves several steps, each of which is crucial for ensuring the security of your IoT devices. Below is a detailed guide to help you through the process:
Step 1: Generate SSH Keys
The first step in setting up SSH keys is to generate them on your local machine. This can be done using the following command:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com"
This command generates an RSA key pair with a key size of 4096 bits and associates it with your email address for identification purposes.
Step 2: Copy Public Key
Once the keys have been generated, the next step is to copy the public key to your Raspberry Pi. This can be done using the ssh-copy-id command:
ssh-copy-id pi@raspberrypi.local
This command copies the public key to the Raspberry Pi, allowing it to authenticate your local machine without requiring a password.
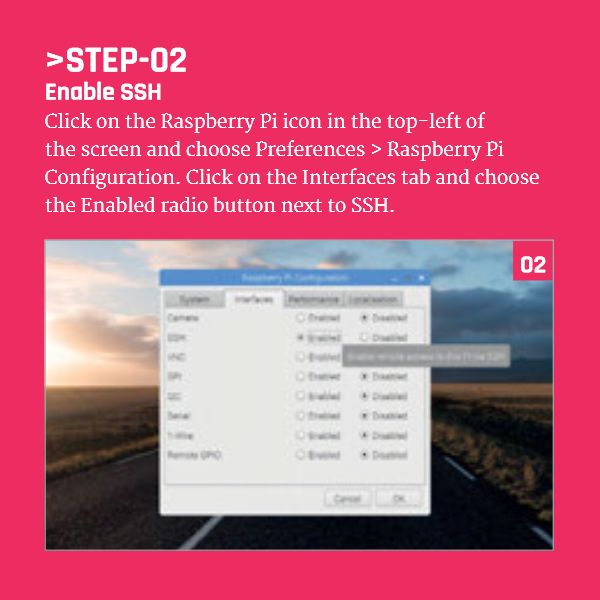
Step 3: Configure Raspberry Pi
After copying the public key, it's important to configure Raspberry Pi to use SSH keys for authentication. This can be done by editing the SSH configuration file:
sudo nano /etc/ssh/sshd_config
Ensure that the following lines are uncommented and set to "yes":
PubkeyAuthentication yesAuthorizedKeysFile .ssh/authorized_keys
Once the configuration is complete, restart the SSH service to apply the changes:
sudo systemctl restart ssh
Securing Your RemoteIoT Platform
In addition to setting up SSH keys, there are several other steps you can take to secure your RemoteIoT platform:
- Update Firmware Regularly: Ensure that your Raspberry Pi and all connected devices are running the latest firmware to protect against vulnerabilities.
- Use Strong Passwords: While SSH keys eliminate the need for passwords, it's still important to use strong passwords for other accounts and services.
- Enable Firewall: Configure a firewall on your Raspberry Pi to restrict access to unauthorized devices.
Troubleshooting Common Issues
Despite following the steps outlined above, you may encounter issues when setting up SSH keys on Raspberry Pi. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH service is running on your Raspberry Pi and that the correct IP address is being used.
- Permission Denied: Verify that the public key has been correctly copied to the Raspberry Pi and that the SSH configuration file has been properly edited.
Best Practices for SSH Keys
To ensure the security of your SSH keys, it's important to follow these best practices:
- Store Private Keys Securely: Keep your private key in a secure location and avoid sharing it with others.
- Use Passphrases: Protect your private key with a passphrase to add an extra layer of security.
- Regularly Rotate Keys: Periodically regenerate and replace your SSH keys to minimize the risk of compromise.
Case Studies
Several organizations have successfully implemented SSH keys on Raspberry Pi to secure their IoT devices. For example, a smart agriculture company used SSH keys to manage remote sensors, ensuring that sensitive data remained protected. Another case involves a healthcare provider using SSH keys to secure medical devices, enhancing patient safety and data privacy.
Future Trends in IoT Security
As IoT technology continues to evolve, so too will the methods used to secure it. Some of the emerging trends in IoT security include:
- Quantum Cryptography: The use of quantum mechanics to create unbreakable encryption methods.
- AI-Driven Security: The integration of artificial intelligence to detect and respond to security threats in real time.
Conclusion
In conclusion, securing your IoT devices using SSH keys on Raspberry Pi is a critical step in protecting against unauthorized access. By following the steps outlined in this guide, you can ensure that your RemoteIoT platform remains secure and functional. Remember to adhere to best practices and stay informed about the latest trends in IoT security.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT technology and security.