Mastering SSH IoT AWS: A Comprehensive Guide For Your Projects
SSH IoT AWS has emerged as a powerful combination for developers looking to securely manage IoT devices in the cloud. This technology leverages the capabilities of AWS to provide robust solutions for IoT applications. By integrating SSH with AWS IoT, developers can ensure secure communication, remote access, and efficient device management. In this article, we will delve into the intricacies of SSH IoT AWS and explore how it can enhance your IoT projects.
As the Internet of Things (IoT) continues to grow, so does the need for secure and scalable solutions. AWS offers a comprehensive suite of services that cater to IoT needs, including secure shell (SSH) functionalities. This combination not only simplifies device management but also ensures data security and reliability. Whether you're a beginner or an experienced developer, understanding SSH IoT AWS is essential for modern IoT applications.
This article aims to provide a detailed overview of SSH IoT AWS, covering its functionalities, benefits, and practical applications. By the end of this guide, you will have a solid understanding of how to implement SSH IoT AWS in your projects and enhance your IoT ecosystem. Let's dive in!
Read also:Olivia Rodrigo Nudes Debunking The Rumors Understanding Privacy And Exploring Olivia Rodrigos Rise To Fame
Table of Contents
- Introduction to SSH IoT AWS
- Benefits of Using SSH IoT AWS
- Setting Up SSH IoT AWS
- Securing IoT Devices with SSH
- AWS IoT Core Integration
- Advanced Features of SSH IoT AWS
- Best Practices for SSH IoT AWS
- Common Challenges and Solutions
- Real-World Applications
- Future Trends in SSH IoT AWS
Introduction to SSH IoT AWS
SSH IoT AWS is a technology that combines secure shell (SSH) protocols with Amazon Web Services (AWS) to create a secure and scalable environment for IoT devices. This integration allows developers to manage IoT devices remotely, ensuring secure communication and data transfer. By leveraging AWS IoT Core and other AWS services, SSH IoT AWS provides a robust solution for managing IoT ecosystems.
Why SSH is Important in IoT?
SSH plays a critical role in IoT by providing secure access to devices over unsecured networks. It encrypts data during transmission, ensuring that sensitive information remains protected. With the increasing number of IoT devices, the need for secure protocols like SSH has become more important than ever.
How AWS Enhances IoT Security?
AWS offers a range of services that enhance IoT security, including AWS IoT Core, AWS IoT Device Defender, and AWS IoT Greengrass. These services work together to provide end-to-end security for IoT devices, ensuring that data is protected at every stage of transmission.
Benefits of Using SSH IoT AWS
There are numerous benefits to using SSH IoT AWS in your IoT projects. From enhanced security to improved scalability, this technology offers a range of advantages that can significantly improve your IoT ecosystem.
Enhanced Security
- SSH ensures secure communication between devices and the cloud.
- Data encryption protects sensitive information during transmission.
- Authentication mechanisms ensure only authorized users can access devices.
Scalability
- AWS IoT Core supports millions of devices, making it ideal for large-scale IoT projects.
- Automatic scaling ensures your system can handle increased traffic and device connections.
Setting Up SSH IoT AWS
Setting up SSH IoT AWS involves several steps, including configuring AWS services, setting up SSH keys, and connecting IoT devices. Below is a step-by-step guide to help you get started:
Step 1: Configure AWS IoT Core
Begin by setting up AWS IoT Core, which serves as the central hub for managing IoT devices. This involves creating a thing, defining policies, and configuring rules.
Read also:Sophie Rain Ed S A Rising Star In The Entertainment Industry
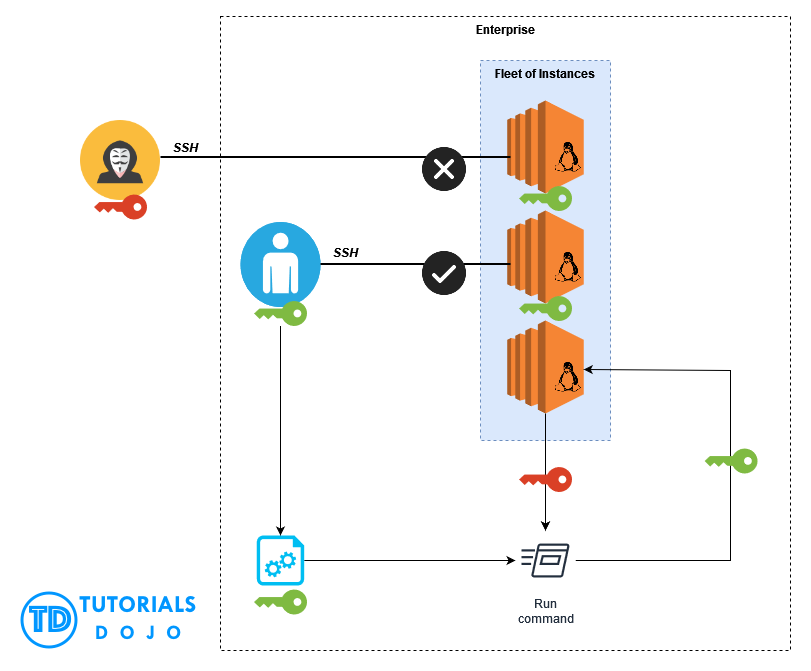
Step 2: Generate SSH Keys
Create SSH keys to ensure secure access to your IoT devices. These keys will be used for authentication when connecting to devices via SSH.
Step 3: Connect IoT Devices
Once AWS IoT Core is configured and SSH keys are generated, connect your IoT devices to the cloud. This involves installing the necessary software and configuring device settings.
Securing IoT Devices with SSH
Securing IoT devices is crucial for protecting sensitive data and ensuring system integrity. SSH provides a secure method for accessing IoT devices, reducing the risk of unauthorized access and data breaches.
Key Security Features of SSH
- Data encryption ensures that all communication is secure.
- Public-key authentication provides a secure method for user verification.
- Firewall integration restricts access to authorized users only.
AWS IoT Core Integration
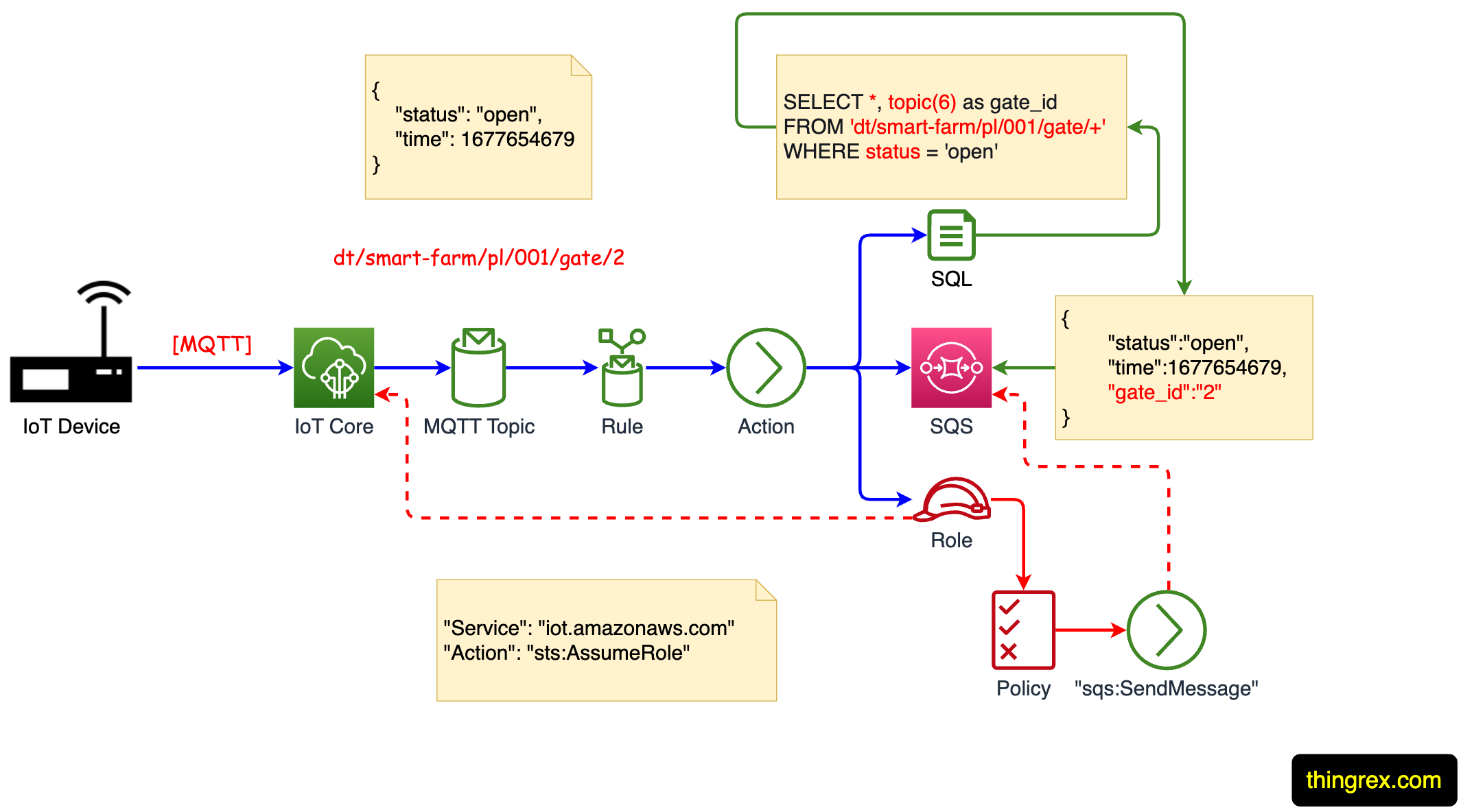
AWS IoT Core is a managed cloud service that allows connected devices to interact securely with cloud applications and other devices. By integrating SSH with AWS IoT Core, developers can create a secure and scalable IoT ecosystem.
How AWS IoT Core Works
AWS IoT Core uses MQTT, HTTP, and WebSockets protocols to facilitate communication between devices and the cloud. It also provides features like device shadows, which allow developers to synchronize device state information.
Advanced Features of SSH IoT AWS
Beyond basic functionality, SSH IoT AWS offers several advanced features that enhance its capabilities. These features include automated device management, data analytics, and machine learning integration.
Automated Device Management
AWS IoT Device Management simplifies the process of managing large fleets of IoT devices. It provides features like over-the-air updates, device monitoring, and group management.
Data Analytics
AWS IoT Analytics allows developers to process and analyze IoT data, providing valuable insights for improving system performance and decision-making.
Best Practices for SSH IoT AWS
To ensure the success of your SSH IoT AWS projects, it's important to follow best practices. These practices include securing devices, optimizing performance, and maintaining system integrity.
Securing Devices
- Use strong passwords and SSH keys for authentication.
- Regularly update device firmware to address security vulnerabilities.
- Implement firewalls and network segmentation to restrict access.
Optimizing Performance
- Monitor device performance and address bottlenecks promptly.
- Use caching and load balancing to improve system efficiency.
Common Challenges and Solutions
While SSH IoT AWS offers numerous benefits, there are challenges that developers may encounter. Below are some common challenges and their solutions:
Challenge: Device Compatibility
Solution: Use AWS IoT Device SDK to ensure compatibility across different devices and platforms.
Challenge: Security Breaches
Solution: Implement multi-factor authentication and regularly audit device security settings.
Real-World Applications
SSH IoT AWS is used in various industries, including healthcare, manufacturing, and smart cities. Below are some real-world applications of this technology:
Healthcare
SSH IoT AWS is used to manage medical devices, ensuring secure data transmission and remote monitoring of patient health.
Manufacturing
In manufacturing, SSH IoT AWS is used for predictive maintenance, reducing downtime and improving operational efficiency.
Future Trends in SSH IoT AWS
The future of SSH IoT AWS looks promising, with advancements in technology driving innovation in IoT applications. Some trends to watch include:
Edge Computing
Edge computing will play a significant role in IoT, allowing data processing to occur closer to the source, reducing latency and improving performance.
Artificial Intelligence
AI integration will enhance IoT capabilities, enabling smarter decision-making and automation in various industries.
Conclusion
In conclusion, SSH IoT AWS offers a powerful solution for managing IoT devices securely and efficiently. By leveraging AWS services and SSH protocols, developers can create robust IoT ecosystems that meet the demands of modern applications. To get the most out of SSH IoT AWS, it's important to follow best practices, address common challenges, and stay updated with the latest trends.
We invite you to explore the possibilities of SSH IoT AWS in your projects. Feel free to leave a comment or share this article with others who may benefit from it. For more information on SSH IoT AWS and related topics, explore our other articles on our website.
Data Source: AWS IoT Documentation