Remote Access To IoT AWS: A Comprehensive Guide For Secure And Efficient Connectivity
In today's interconnected world, remote access to IoT AWS has become a crucial aspect of modern technology infrastructure. As businesses increasingly rely on IoT devices to enhance productivity and streamline operations, ensuring secure and efficient remote access has never been more important. This article will explore the intricacies of remote access to IoT AWS, providing you with actionable insights and best practices.
Remote access to IoT AWS enables organizations to manage and monitor their IoT devices from anywhere in the world. Whether you're a small business or a large enterprise, understanding how to implement secure remote access is essential for maintaining data integrity and operational efficiency.
By the end of this guide, you'll have a clear understanding of the technologies, tools, and strategies involved in setting up and managing remote access to IoT AWS. Let's dive into the details and discover how you can optimize your IoT infrastructure for success.
Read also:What Celebrities Live In Sedona A Comprehensive Guide To The Starstudded Desert Retreat
Table of Contents
- Introduction to Remote Access to IoT AWS
- Understanding IoT and AWS Basics
- Remote Access Methods for IoT AWS
- Security Considerations for Remote Access
- Tools and Technologies for Remote Access
- Best Practices for Implementing Remote Access
- Scalability of Remote Access Solutions
- Case Studies: Real-World Applications
- Troubleshooting Common Issues
- Conclusion and Next Steps
Introduction to Remote Access to IoT AWS
Remote access to IoT AWS refers to the ability to connect to and manage IoT devices hosted on Amazon Web Services (AWS) from remote locations. This technology enables organizations to monitor and control their IoT infrastructure without being physically present at the site. By leveraging AWS's robust cloud platform, businesses can ensure seamless connectivity and data management.
In this section, we will explore the fundamental concepts of remote access and its significance in the context of IoT AWS. We'll also discuss the benefits of implementing remote access solutions and how they contribute to operational efficiency.
Why Remote Access to IoT AWS Matters
With the rapid growth of IoT devices, the demand for secure and reliable remote access has surged. Organizations need to ensure that their IoT infrastructure remains accessible and manageable, regardless of geographical location. Remote access to IoT AWS offers several advantages:
- Enhanced operational flexibility
- Improved data accessibility
- Reduced downtime and maintenance costs
- Increased security and control
Understanding IoT and AWS Basics
Before diving into the specifics of remote access to IoT AWS, it's essential to understand the basics of IoT and AWS. IoT, or the Internet of Things, refers to a network of interconnected devices capable of exchanging data. AWS, on the other hand, is a cloud computing platform that provides scalable infrastructure for hosting and managing IoT applications.
Key Components of IoT AWS
Here are some key components of IoT AWS that play a critical role in enabling remote access:
- AWS IoT Core: A managed cloud service for connecting IoT devices
- AWS Lambda: A serverless computing service for executing code in response to events
- Amazon S3: A cloud storage service for storing and retrieving IoT data
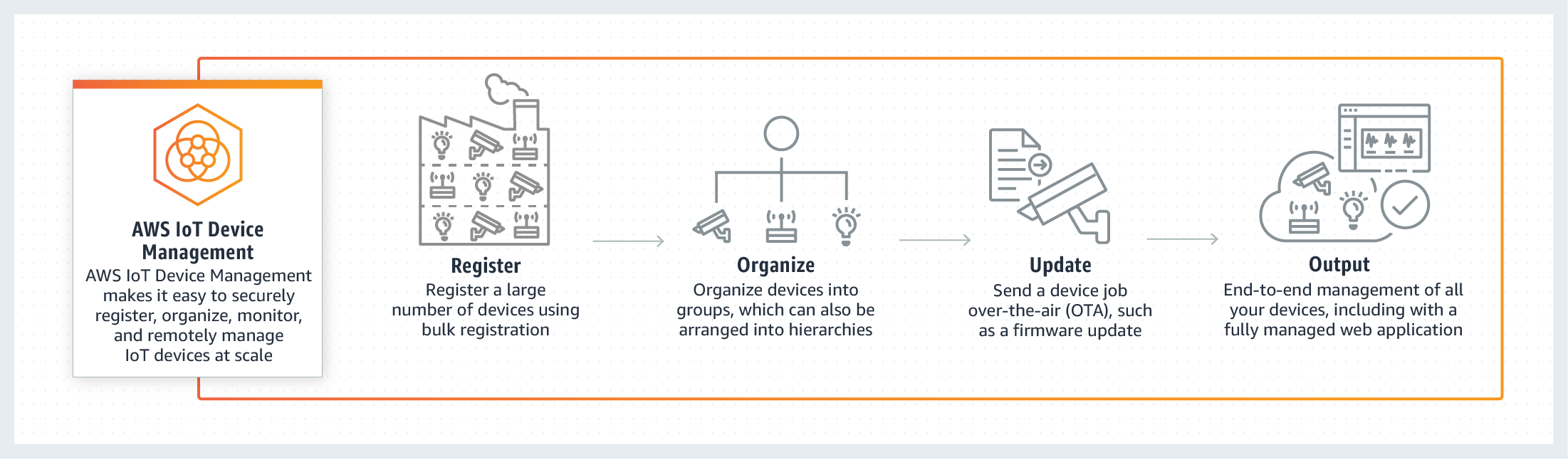
- AWS IoT Device Management: A service for managing IoT devices at scale
Remote Access Methods for IoT AWS
There are several methods for achieving remote access to IoT AWS. Each method has its own set of advantages and limitations, and the choice of method depends on the specific requirements of your organization. Below, we will discuss some of the most common remote access methods:
Read also:Kylie Kelce And Jason Kelce A Closer Look At Their Lives Achievements And Relationships
1. SSH Tunneling
SSH tunneling is a secure method for accessing IoT devices hosted on AWS. It involves creating an encrypted connection between the local machine and the remote server, ensuring that data transmitted over the network remains secure.
2. AWS IoT Core MQTT
AWS IoT Core supports the MQTT protocol, which is widely used for IoT communication. By leveraging MQTT, organizations can establish secure and efficient remote access to their IoT devices.
Security Considerations for Remote Access
Security is a top priority when implementing remote access to IoT AWS. Organizations must ensure that their IoT infrastructure is protected from unauthorized access and cyber threats. Below are some key security considerations to keep in mind:
Authentication and Authorization
Implementing strong authentication and authorization mechanisms is crucial for securing remote access. AWS provides several tools, such as AWS Identity and Access Management (IAM), to help organizations manage access to their IoT resources.
Encryption
Encrypting data in transit and at rest is essential for maintaining data confidentiality. AWS offers various encryption options, including SSL/TLS for securing communication between devices and the cloud.
Tools and Technologies for Remote Access
Several tools and technologies can facilitate remote access to IoT AWS. These tools help organizations manage their IoT infrastructure more effectively and securely. Below are some of the most popular tools:
AWS IoT Device Defender
AWS IoT Device Defender is a service that monitors the security of IoT devices and alerts administrators to potential threats. It provides visibility into device behavior and helps organizations maintain compliance with security best practices.
AWS CloudFormation
AWS CloudFormation is a service that enables organizations to automate the deployment of IoT infrastructure. By using CloudFormation templates, businesses can streamline the setup process and ensure consistency across their IoT deployments.
Best Practices for Implementing Remote Access
Implementing remote access to IoT AWS requires careful planning and execution. Below are some best practices to follow when setting up remote access:
Plan Your Architecture
Designing a robust architecture is the first step in implementing remote access. Consider factors such as scalability, security, and performance when planning your IoT infrastructure.
Monitor and Maintain
Regular monitoring and maintenance are essential for ensuring the reliability and security of your IoT infrastructure. Use tools like AWS CloudWatch to monitor system performance and identify potential issues.
Scalability of Remote Access Solutions
Scalability is a critical factor when implementing remote access to IoT AWS. As your IoT infrastructure grows, you'll need to ensure that your remote access solution can handle the increasing demand. AWS provides several features to help organizations scale their IoT deployments:
Auto Scaling
AWS Auto Scaling allows organizations to automatically adjust the capacity of their IoT infrastructure based on demand. This ensures that resources are allocated efficiently and cost-effectively.
Case Studies: Real-World Applications
Several organizations have successfully implemented remote access to IoT AWS in their operations. Below are some case studies that demonstrate the benefits of this technology:
Case Study 1: Smart Agriculture
Agricultural companies are using IoT devices to monitor soil moisture, temperature, and other environmental factors. By implementing remote access to IoT AWS, these companies can manage their IoT infrastructure more effectively and make data-driven decisions.
Troubleshooting Common Issues
While remote access to IoT AWS offers many benefits, it can also present challenges. Below are some common issues and their solutions:
Connection Problems
If you're experiencing connection issues, check your network settings and ensure that your devices are properly configured. Additionally, verify that your AWS credentials are correct and up to date.
Conclusion and Next Steps
In conclusion, remote access to IoT AWS is a powerful tool for managing and monitoring IoT devices. By following the best practices outlined in this guide and leveraging the tools and technologies provided by AWS, organizations can ensure secure and efficient remote access to their IoT infrastructure.
We encourage you to take the next step by exploring AWS's offerings and experimenting with remote access solutions for your IoT devices. Don't forget to share your thoughts and experiences in the comments section below. For more information on IoT and AWS, check out our other articles on the topic.
References: