Securely Connect Remote IoT VPC Raspberry Pi Download Windows: A Comprehensive Guide
As the Internet of Things (IoT) continues to evolve, securely connecting remote devices has become a top priority for businesses and individuals alike. Whether you're managing a network of IoT devices or setting up a Raspberry Pi for remote access, ensuring security is essential. This guide will walk you through the steps to securely connect a remote IoT VPC using Raspberry Pi and provide insights into downloading necessary configurations for Windows.
With the increasing reliance on connected devices, the risks associated with insecure networks are growing exponentially. A secure connection not only protects your data but also ensures the smooth operation of your IoT infrastructure. This article will explore the best practices, tools, and configurations to help you achieve this goal.
Whether you're a tech enthusiast, a professional IT administrator, or a small business owner, this guide will provide actionable insights into setting up a secure VPC (Virtual Private Cloud) environment for your IoT devices using Raspberry Pi and ensuring compatibility with Windows systems.
Read also:Comprehensive Guide To Modesto Gang Map Understanding The Dynamics And Challenges
Understanding IoT Security and Its Importance
Why IoT Security Matters
In today's interconnected world, IoT devices play a crucial role in various industries, from healthcare to manufacturing. However, the proliferation of these devices has also increased the attack surface for cybercriminals. According to a report by Symantec, over 50% of IoT devices are vulnerable to medium or high-severity attacks. This highlights the importance of implementing robust security measures when connecting remote IoT devices.
Key reasons why IoT security matters include:
- Protecting sensitive data from unauthorized access.
- Ensuring device integrity and preventing malicious tampering.
- Maintaining system reliability and uptime.
Common IoT Security Challenges
Despite the growing awareness of IoT security, many organizations still face significant challenges. Some of the most common issues include:
- Lack of standardized security protocols.
- Weak authentication mechanisms.
- Inadequate encryption for data transmission.
To address these challenges, it's essential to adopt a proactive approach to IoT security, starting with the basics of network configuration and device management.
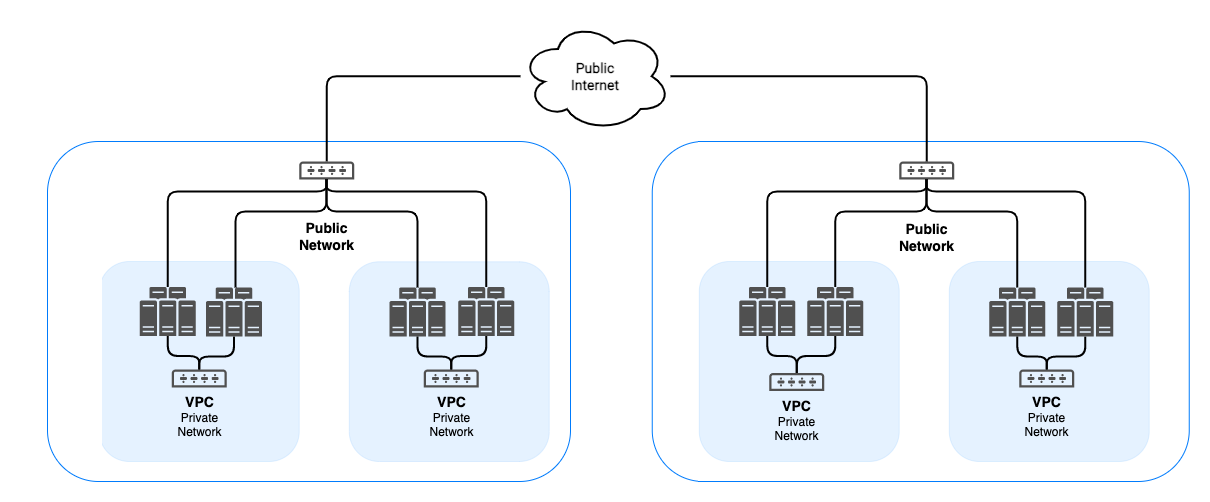
Setting Up a Secure VPC Environment
What Is a VPC?
A Virtual Private Cloud (VPC) is a dedicated network environment that provides secure and isolated connectivity for your IoT devices. By creating a VPC, you can control access to your devices and ensure that only authorized users can interact with them. This is particularly important when dealing with remote IoT deployments.
Steps to Configure a VPC
Configuring a VPC involves several key steps:
Read also:David Belen Rivera The Rising Star In The Entertainment Industry
- Define your network topology and allocate IP addresses.
- Set up subnets and route tables to manage traffic flow.
- Implement security groups and network access control lists (ACLs) to restrict access.
For example, AWS provides a user-friendly interface for setting up VPCs, allowing you to configure advanced security features such as NAT gateways and VPN connections.
Using Raspberry Pi for Remote IoT Connections
Why Choose Raspberry Pi?
Raspberry Pi is a popular choice for IoT projects due to its affordability, flexibility, and ease of use. With its lightweight operating system and versatile hardware, Raspberry Pi can serve as a secure gateway for connecting remote IoT devices. Additionally, it supports a wide range of protocols and libraries, making it ideal for custom configurations.
Setting Up Raspberry Pi for IoT
To use Raspberry Pi for remote IoT connections, follow these steps:
- Install the latest version of Raspberry Pi OS on your device.
- Enable SSH (Secure Shell) for remote access and configure firewall rules.
- Install necessary libraries and dependencies for your IoT application.
For example, you can use Python libraries such as MQTT or CoAP to facilitate communication between your Raspberry Pi and IoT devices.
Securing IoT Connections with Raspberry Pi
Best Practices for IoT Security
Securing IoT connections requires a combination of hardware and software measures. Some best practices include:
- Using strong passwords and enabling two-factor authentication (2FA).
- Regularly updating firmware and software to patch vulnerabilities.
- Encrypting data transmissions using protocols like TLS or SSL.
By following these practices, you can significantly reduce the risk of unauthorized access and data breaches.
Implementing Encryption on Raspberry Pi
To implement encryption on Raspberry Pi, you can use tools such as OpenSSL or GPG. These tools allow you to generate secure keys and certificates for encrypting data transmissions. Additionally, you can configure Raspberry Pi to use secure protocols such as HTTPS or SSH for remote access.
Downloading IoT Configurations for Windows
Compatibility with Windows Systems
When working with IoT devices, ensuring compatibility with Windows systems is crucial. Fortunately, many IoT platforms and tools offer seamless integration with Windows, allowing you to manage your devices from a centralized location. For example, Microsoft Azure IoT provides a comprehensive suite of tools for managing IoT devices, including support for Windows environments.
Steps to Download IoT Configurations
To download IoT configurations for Windows, follow these steps:
- Install the necessary drivers and software on your Windows system.
- Connect to your IoT devices using a secure protocol such as SSH or HTTPS.
- Download the required configurations and apply them to your devices.
For example, you can use tools like PuTTY or WinSCP to securely transfer files between your Windows system and IoT devices.
Tools and Software for IoT Security
Recommended Tools
Several tools and software solutions are available to enhance IoT security. Some popular options include:
- Wireshark: A network protocol analyzer for monitoring and analyzing traffic.
- Snort: An intrusion detection and prevention system for securing networks.
- OpenSSL: A robust toolkit for implementing encryption and secure communications.
These tools can help you identify potential vulnerabilities and implement effective security measures.
Software Libraries for IoT Development
When developing IoT applications, using reliable software libraries is essential. Some recommended libraries include:
- MQTT: A lightweight messaging protocol for IoT devices.
- CoAP: A specialized web transfer protocol for constrained devices.
- Node-RED: A visual tool for wiring together hardware devices and APIs.
These libraries simplify the development process and ensure compatibility with various platforms.
Best Practices for Managing IoT Devices
Device Management Strategies
Effective device management is critical for maintaining a secure IoT environment. Some best practices include:
- Regularly monitoring device activity and performance metrics.
- Implementing automated updates and patches for firmware and software.
- Segmenting devices into separate networks to minimize the impact of potential breaches.
By adopting these strategies, you can ensure the long-term security and reliability of your IoT infrastructure.
Remote Monitoring and Maintenance
Remote monitoring and maintenance are essential for managing IoT devices in real-time. Tools like Azure IoT Hub and AWS IoT Core provide advanced features for monitoring device health, managing configurations, and troubleshooting issues. These platforms also offer scalable solutions for handling large-scale IoT deployments.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT VPC Raspberry Pi download windows requires a combination of robust security measures, proper network configuration, and effective device management. By following the best practices outlined in this guide, you can create a secure and reliable IoT environment that meets your specific needs.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT security and related topics. Together, let's build a safer and more connected world!
Table of Contents
- Understanding IoT Security and Its Importance
- Setting Up a Secure VPC Environment
- Using Raspberry Pi for Remote IoT Connections
- Securing IoT Connections with Raspberry Pi
- Downloading IoT Configurations for Windows
- Tools and Software for IoT Security
- Best Practices for Managing IoT Devices