Comprehensive Guide To IoT Device SSH Access On Windows 10
In the era of interconnected devices, IoT (Internet of Things) has transformed how we interact with technology. Accessing IoT devices remotely via SSH (Secure Shell) on Windows 10 is a powerful method for managing and monitoring these devices securely. Whether you're a tech enthusiast or a professional, understanding how to configure and use SSH for IoT devices is essential for enhancing productivity and ensuring robust cybersecurity.
As IoT continues to expand, the need for secure communication channels becomes increasingly important. SSH access provides an encrypted connection, safeguarding sensitive data and commands from unauthorized access. This guide delves deep into the process of setting up and utilizing SSH for IoT devices on Windows 10, ensuring that you have all the necessary tools and knowledge at your disposal.
Through this article, we aim to provide a step-by-step process that simplifies the complex task of configuring SSH access for IoT devices. By following our expert-recommended practices, you can enhance your device management capabilities while maintaining top-tier security standards. Let's dive into the world of IoT and discover how SSH can revolutionize the way you interact with your devices.
Read also:Hdhub4u Tv Your Ultimate Destination For South Hindi Dubbed Movies
Table of Contents
- Introduction to SSH
- Why Use SSH for IoT Devices?
- Prerequisites for SSH Access
- Step-by-Step SSH Configuration on Windows 10
- Securing SSH Connections
- Troubleshooting Common SSH Issues
- Optimizing SSH Performance
- Advanced SSH Features for IoT Devices
- Real-World Use Cases of SSH in IoT
- Conclusion and Next Steps
Introduction to SSH
SSH, or Secure Shell, is a protocol that facilitates secure communication between two devices over an unsecured network. It encrypts all data exchanged between the client and the server, making it an ideal choice for managing IoT devices remotely. With SSH, you can execute commands, transfer files, and monitor device performance without compromising security.
One of the key benefits of SSH is its ability to authenticate users securely using public key cryptography. This ensures that only authorized users can access your IoT devices, minimizing the risk of unauthorized access and data breaches. Additionally, SSH supports various authentication methods, including passwords, public keys, and even two-factor authentication (2FA).
How Does SSH Work?
SSH operates on a client-server model. The client initiates the connection, while the server responds by authenticating the client and establishing a secure session. Once the connection is established, users can interact with the server through a command-line interface or graphical user interface, depending on the application.
- Encryption: SSH encrypts all data transmitted between the client and server, ensuring confidentiality and integrity.
- Authentication: Users must authenticate themselves before gaining access to the server, adding an extra layer of security.
- Portability: SSH is compatible with multiple platforms, including Windows, Linux, and macOS, making it a versatile choice for IoT device management.
Why Use SSH for IoT Devices?
IoT devices are becoming increasingly prevalent in both personal and professional environments. However, their widespread adoption also makes them prime targets for cyberattacks. Using SSH for IoT device management offers several advantages that enhance security and efficiency:
- Enhanced Security: SSH encrypts all communication, protecting sensitive data from interception and unauthorized access.
- Remote Access: With SSH, you can manage IoT devices from anywhere, as long as you have an internet connection.
- Automation: SSH enables the execution of automated scripts, streamlining repetitive tasks and reducing manual effort.
- Scalability: SSH supports multiple devices and users, making it suitable for large-scale IoT deployments.
By leveraging SSH, you can ensure that your IoT devices remain secure while maximizing their functionality and usability.
Prerequisites for SSH Access
Before configuring SSH access for IoT devices on Windows 10, it's essential to ensure that your system meets the necessary requirements. Here's a list of prerequisites:
Read also:Where Does Sandra Bullock Live Exploring The Life And Luxurious Homes Of The Hollywood Star
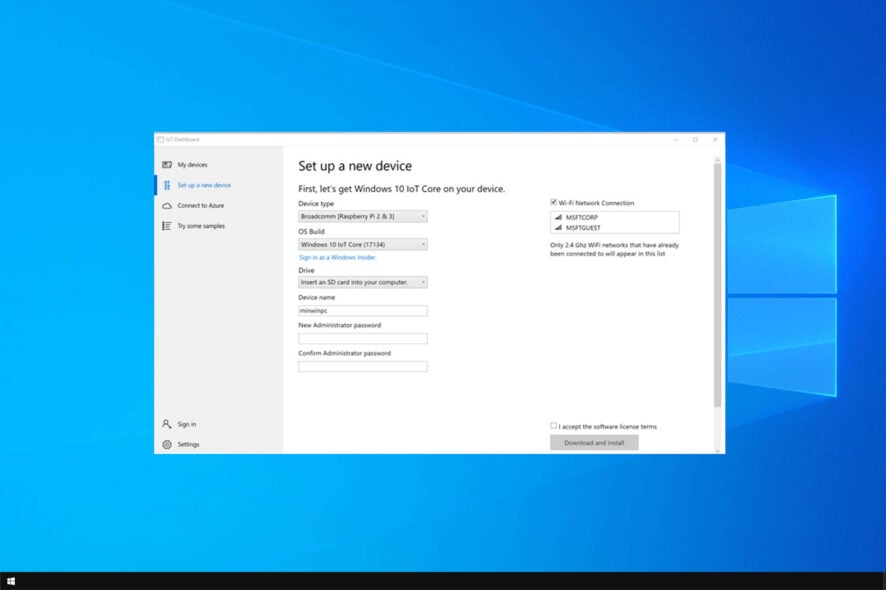
- Windows 10 Version: Ensure that you're running Windows 10 Build 17063 or later, as earlier versions may not support SSH natively.
- OpenSSH Client: Install the OpenSSH client on your Windows 10 machine. This can be done through the Windows Features settings or PowerShell.
- IoT Device Configuration: Verify that your IoT device is properly configured and accessible via SSH. Check the device's documentation for specific setup instructions.
- Network Connectivity: Ensure that both your Windows 10 machine and IoT device are connected to the same network or have a secure connection established through a virtual private network (VPN).
By meeting these prerequisites, you'll be well-prepared to set up SSH access for your IoT devices.
Step-by-Step SSH Configuration on Windows 10
Configuring SSH access on Windows 10 is a straightforward process. Follow these steps to establish a secure connection with your IoT devices:
Step 1: Enable OpenSSH Client
Open the Windows Settings app and navigate to "Apps"> "Optional Features." Click on "Add a Feature" and search for "OpenSSH Client." Install the feature if it's not already enabled.
Step 2: Verify SSH Client Installation
Open PowerShell or Command Prompt and type the following command to verify that the OpenSSH client is installed:
ssh -V
This command will display the installed SSH version, confirming that the client is ready for use.
Step 3: Connect to Your IoT Device
Use the following command to establish an SSH connection with your IoT device:
ssh username@device_ip_address
Replace "username" with your IoT device's login credentials and "device_ip_address" with the device's IP address.
Securing SSH Connections
While SSH provides a secure communication channel, it's crucial to implement additional security measures to protect your IoT devices:
- Disable Password Authentication: Use public key authentication instead of passwords to prevent brute-force attacks.
- Change Default Port: Modify the default SSH port (22) to a non-standard port to reduce the risk of automated attacks.
- Limit User Access: Restrict SSH access to specific users or IP addresses using firewall rules or SSH configuration files.
- Enable Logging: Configure SSH to log all connection attempts, enabling you to monitor and detect suspicious activities.
By implementing these security best practices, you can significantly enhance the protection of your IoT devices.
Troubleshooting Common SSH Issues
Encountering issues while configuring SSH access is not uncommon. Here are some common problems and their solutions:
- Connection Refused: Ensure that the SSH service is running on the IoT device and that the firewall allows incoming connections on the specified port.
- Authentication Failure: Double-check your login credentials and ensure that the public key is correctly added to the device's authorized_keys file.
- Timeout Errors: Verify that both devices are connected to the same network or have a stable internet connection.
If the issue persists, consult the device's documentation or seek assistance from the manufacturer's support team.
Optimizing SSH Performance
To ensure optimal performance when using SSH for IoT device management, consider the following tips:
- Compress Data: Enable data compression in the SSH configuration file to reduce transmission time.
- Use Efficient Ciphers: Select lightweight encryption algorithms that balance security and performance.
- Limit Idle Timeouts: Configure idle timeouts to disconnect inactive sessions, freeing up system resources.
By optimizing SSH performance, you can improve the responsiveness and efficiency of your IoT device management processes.
Advanced SSH Features for IoT Devices
SSH offers several advanced features that can enhance your IoT device management capabilities:
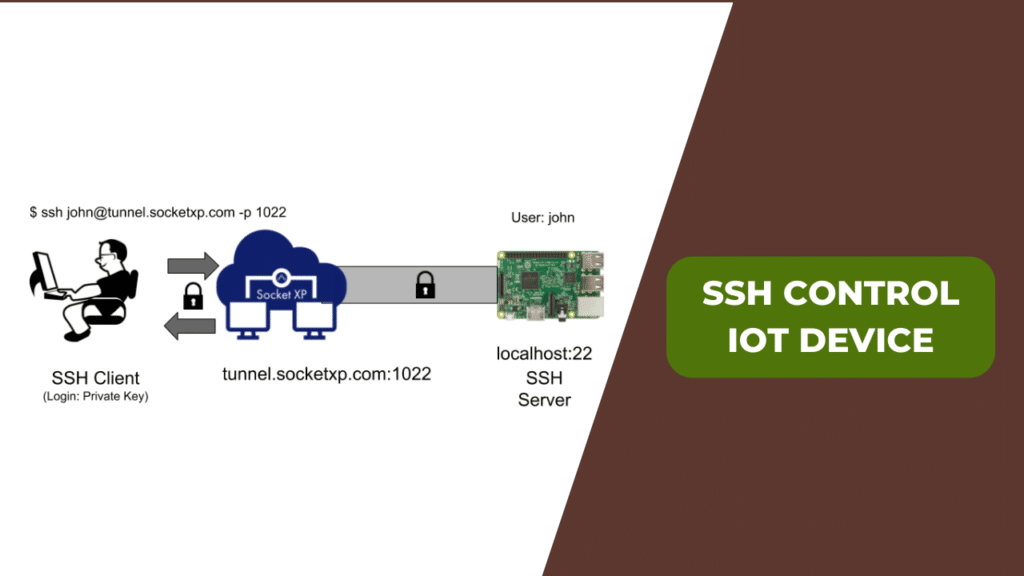
SSH Tunneling
SSH tunneling allows you to securely forward network traffic between devices, enabling access to services that are otherwise restricted or blocked.
SSH Port Forwarding
Port forwarding enables you to map local ports to remote services, facilitating seamless communication between devices.
By exploring these advanced features, you can unlock new possibilities for managing and interacting with your IoT devices.
Real-World Use Cases of SSH in IoT
SSH is widely used in various industries for IoT device management. Here are some real-world examples:
- Smart Home Automation: SSH allows homeowners to remotely control and monitor smart home devices, enhancing convenience and security.
- Industrial IoT: Manufacturers use SSH to manage and maintain industrial IoT devices, ensuring smooth operations and minimizing downtime.
- Healthcare IoT: SSH provides secure access to medical IoT devices, safeguarding patient data and enabling remote monitoring.
These use cases demonstrate the versatility and importance of SSH in modern IoT applications.
Conclusion and Next Steps
In conclusion, SSH access for IoT devices on Windows 10 offers a secure and efficient method for managing and monitoring these devices. By following the steps outlined in this guide, you can configure SSH access with confidence, ensuring that your IoT devices remain protected and functional.
We encourage you to explore the advanced features of SSH and implement additional security measures to further enhance your IoT device management capabilities. Don't forget to share your thoughts and experiences in the comments section below. Additionally, consider exploring other articles on our site to expand your knowledge of IoT and cybersecurity.
For further reading, refer to the following resources: