RemoteIoT Platform SSH Key Not Working: Comprehensive Guide To Troubleshooting And Solutions
RemoteIoT platform has become a cornerstone for managing and monitoring IoT devices remotely. However, encountering issues such as the SSH key not working can hinder your operations. In this article, we will delve into the common reasons why this problem occurs and provide effective solutions to resolve it.
As more organizations adopt IoT technologies, the need for secure and efficient remote management tools has grown exponentially. The RemoteIoT platform is designed to facilitate seamless communication and control over IoT devices. However, when the SSH key fails to function, it can disrupt workflows and compromise security.
This guide aims to equip you with the knowledge and tools to troubleshoot and fix SSH key-related issues. Whether you're a beginner or an experienced IoT professional, this article will offer valuable insights and practical solutions to ensure your RemoteIoT platform runs smoothly.
Read also:Celebrities That Live In Sedona Discover The Hidden Gems Of Red Rock Country
Table of Contents
- Introduction to RemoteIoT Platform
- Understanding SSH Keys
- Why SSH Key Fails in RemoteIoT
- Common Issues with SSH Keys
- Troubleshooting Steps for SSH Key Issues
- Advanced Solutions for Persistent Issues
- Security Best Practices for SSH Keys
- Optimizing RemoteIoT Platform Performance
- Tools and Resources for Managing SSH Keys
- Conclusion and Next Steps
Introduction to RemoteIoT Platform
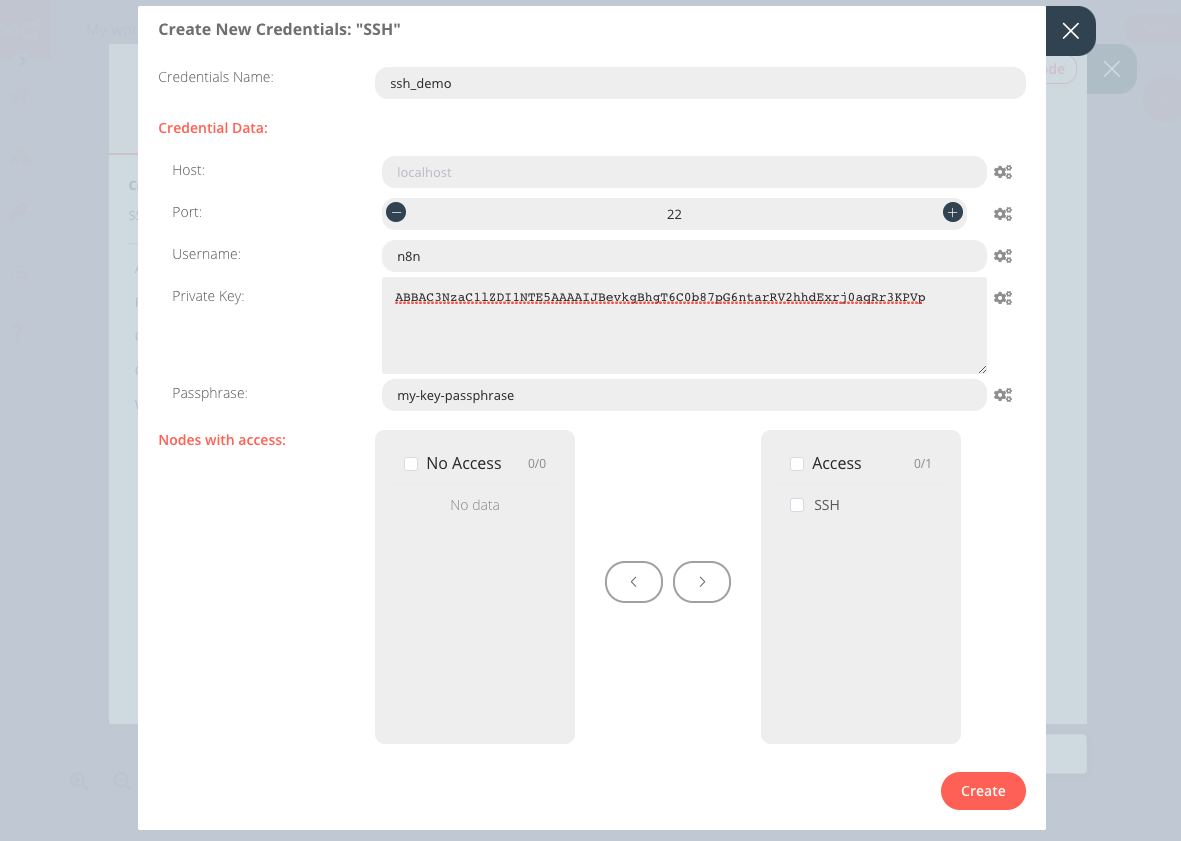
The RemoteIoT platform is a robust solution designed to manage and monitor IoT devices from anywhere in the world. It offers a wide range of features, including real-time data analytics, device configuration, and secure communication protocols. One of the key components of this platform is the use of SSH keys for secure authentication.
SSH keys play a crucial role in ensuring that only authorized users can access the system. They provide a more secure alternative to traditional password-based authentication. However, when the SSH key stops working, it can lead to significant disruptions in operations.
In this section, we will explore the fundamental features of the RemoteIoT platform and its reliance on SSH keys for secure communication.
Understanding SSH Keys
What Are SSH Keys?
SSH keys are cryptographic keys used for authenticating secure connections between a client and a server. They consist of a public key and a private key. The public key is shared with the server, while the private key remains confidential and is stored on the client's device.
How SSH Keys Work
When you attempt to connect to a server using SSH, the server verifies your identity by checking the public key against the private key stored on your device. If the keys match, the connection is established. This process eliminates the need for password-based authentication, reducing the risk of brute-force attacks.
SSH keys are widely used in various industries, including IoT, to secure communications and protect sensitive data.
Read also:Mastering Movierules Your Ultimate Guide To Film Success
Why SSH Key Fails in RemoteIoT
There are several reasons why an SSH key might fail to work in the RemoteIoT platform. These issues can range from simple configuration errors to more complex technical problems. Below, we will discuss the most common causes:
- Expired Keys: SSH keys may have an expiration date, and if they are not renewed, they will stop working.
- Incorrect Key Placement: The public key must be correctly placed in the authorized_keys file on the server.
- File Permissions: Incorrect file permissions on the server can prevent the SSH key from being recognized.
- Server Configuration Issues: Misconfigurations in the SSH server settings can also lead to key failures.
Understanding these potential issues is the first step toward resolving them effectively.
Common Issues with SSH Keys
Key Mismatch
One of the most common issues with SSH keys is a mismatch between the public and private keys. This can occur if the keys are not correctly generated or if they have been altered during transmission.
Corrupted Keys
SSH keys can become corrupted due to file system errors or improper handling. Corrupted keys will not function correctly and must be regenerated.
These issues can be frustrating, but with the right approach, they can be resolved efficiently.
Troubleshooting Steps for SSH Key Issues
When you encounter an SSH key problem in the RemoteIoT platform, follow these steps to troubleshoot the issue:
- Verify Key Placement: Ensure that the public key is correctly placed in the authorized_keys file on the server.
- Check File Permissions: Verify that the file permissions on the server are set correctly for the SSH keys.
- Test the Connection: Use the ssh command to test the connection and identify any errors.
- Regenerate Keys: If the problem persists, consider regenerating the SSH keys and reconfiguring the server.
By following these steps, you can diagnose and fix most SSH key-related issues.
Advanced Solutions for Persistent Issues
In some cases, standard troubleshooting methods may not resolve the issue. Here are some advanced solutions to consider:
- Update SSH Server: Ensure that the SSH server software is up to date and patched against known vulnerabilities.
- Check Firewall Settings: Verify that the firewall is not blocking SSH connections.
- Consult Server Logs: Review the server logs for any error messages that may provide clues to the problem.
These advanced techniques can help resolve even the most stubborn SSH key issues.
Security Best Practices for SSH Keys
Securing your SSH keys is essential to protect your RemoteIoT platform from unauthorized access. Here are some best practices to follow:
- Use Strong Keys: Generate SSH keys with a sufficient key length to ensure their security.
- Protect Private Keys: Store private keys securely and use strong passphrases to protect them.
- Regularly Rotate Keys: Periodically rotate SSH keys to minimize the risk of compromise.
Implementing these security measures will help safeguard your RemoteIoT platform against potential threats.
Optimizing RemoteIoT Platform Performance
To ensure optimal performance of your RemoteIoT platform, consider the following tips:
- Monitor System Logs: Regularly review system logs to identify and address potential issues promptly.
- Automate Routine Tasks: Use automation tools to streamline routine maintenance tasks.
- Stay Updated: Keep your software and firmware up to date to benefit from the latest features and security patches.
By optimizing your platform, you can enhance its efficiency and reliability.
Tools and Resources for Managing SSH Keys
There are several tools and resources available to help you manage SSH keys effectively:
- SSH Keygen: A command-line tool for generating SSH keys.
- SSH Agent: A utility for managing SSH keys and providing authentication credentials.
- Online Tutorials: Numerous online resources provide detailed guides on SSH key management.
Utilizing these tools and resources can simplify the process of managing SSH keys.
Conclusion and Next Steps
In conclusion, SSH key issues in the RemoteIoT platform can be challenging, but with the right approach, they can be resolved effectively. By understanding the common causes of these issues and following the troubleshooting steps outlined in this guide, you can ensure the smooth operation of your RemoteIoT platform.
We encourage you to take the following actions:
- Share your thoughts and experiences in the comments section below.
- Explore other articles on our website for more insights into IoT technologies and security practices.
- Stay informed about the latest developments in the field by subscribing to our newsletter.
Thank you for reading, and we hope this article has provided you with the knowledge and tools to address SSH key issues in your RemoteIoT platform successfully.