Secure Remote Access With Raspberry Pi: A Comprehensive Guide
Remote access technology has become a critical component of modern computing, enabling users to control and manage devices from virtually anywhere. Among the many tools available, Raspberry Pi secure remote access free solutions have gained immense popularity due to their affordability, flexibility, and ease of use. Whether you're a hobbyist, developer, or small business owner, leveraging Raspberry Pi for secure remote access can significantly enhance your productivity and efficiency.
Raspberry Pi is not just a tiny computer; it's a powerful platform that can be configured to provide secure remote access without requiring expensive proprietary software. By setting up your Raspberry Pi correctly, you can create a robust and secure connection to your devices, ensuring data privacy and seamless operations.
This article will guide you through the process of setting up Raspberry Pi for secure remote access, exploring various methods, tools, and best practices. Whether you're new to Raspberry Pi or already familiar with its capabilities, this guide will provide you with the knowledge and resources you need to establish a secure remote access solution.
Read also:Goddess Alexandria The Rise Of A Modern Icon
Table of Contents
- Introduction to Raspberry Pi Secure Remote Access
- Raspberry Pi Basics and Its Role in Remote Access
- Why Secure Remote Access Matters
- Methods for Secure Remote Access on Raspberry Pi
- Setting Up SSH for Secure Remote Access
- Using VNC for Remote Desktop Access
- Creating a Secure Tunnel with a Raspberry Pi VPN
- Best Practices for Securing Your Raspberry Pi
- Troubleshooting Common Issues
- Conclusion and Call to Action
Introduction to Raspberry Pi Secure Remote Access
Understanding Raspberry Pi as a Remote Access Tool
Raspberry Pi has revolutionized the way we think about computing, offering a cost-effective and versatile solution for a wide range of applications. One of its most valuable uses is as a platform for secure remote access. With the right configuration, Raspberry Pi can serve as a gateway to your devices, allowing you to manage and interact with them remotely.
Remote access enables you to perform tasks such as file transfers, system monitoring, and software updates without being physically present. This is particularly beneficial for individuals working in distributed teams or managing multiple devices across different locations.
Benefits of Using Raspberry Pi for Remote Access
Using Raspberry Pi for secure remote access offers several advantages:
- Cost-Effective: Raspberry Pi is affordable, making it an attractive option for individuals and small businesses.
- Flexibility: It supports various protocols and can be customized to meet specific needs.
- Energy Efficient: Raspberry Pi consumes minimal power, making it suitable for long-term use.
- Open Source: The Raspberry Pi ecosystem is supported by a vast community, providing access to countless resources and tutorials.
Raspberry Pi Basics and Its Role in Remote Access
Raspberry Pi is a single-board computer developed by the Raspberry Pi Foundation. It was initially designed as an educational tool but has since evolved into a versatile platform for a wide range of applications. At its core, Raspberry Pi is a compact device that can run various operating systems, including Linux-based distributions like Raspbian.
Components of Raspberry Pi
To understand how Raspberry Pi facilitates secure remote access, it's essential to familiarize yourself with its key components:
- Processor: Raspberry Pi is powered by a Broadcom ARM processor, which provides sufficient computing power for remote access tasks.
- Memory: Depending on the model, Raspberry Pi offers varying amounts of RAM, ranging from 512MB to 8GB.
- Connectivity: Raspberry Pi supports Ethernet, Wi-Fi, and Bluetooth, enabling seamless network connectivity.
- Storage: It uses microSD cards as its primary storage medium, allowing users to install different operating systems.
Why Secure Remote Access Matters
In today's digital age, security is a top priority. When setting up remote access, it's crucial to ensure that your connection is secure to protect sensitive data and prevent unauthorized access. A secure remote access solution helps safeguard your devices and networks from potential threats, such as malware, hacking, and data breaches.
Read also:Best Tax Expert In Tulsa Your Ultimate Guide To Finding The Right Professional
Risks of Insecure Remote Access
Using an insecure remote access method can expose your devices to various risks:
- Data Theft: Hackers can intercept and steal sensitive information transmitted over unsecured networks.
- Unauthorized Access: Weak security measures can allow malicious actors to gain control of your devices.
- Malware Infection: Insecure connections can serve as entry points for malware and other malicious software.
Methods for Secure Remote Access on Raspberry Pi
There are several methods for establishing secure remote access on Raspberry Pi. Each method has its own advantages and disadvantages, depending on your specific needs and requirements.
SSH (Secure Shell)
SSH is one of the most popular and secure methods for remote access. It encrypts all data transmitted between your device and Raspberry Pi, ensuring confidentiality and integrity.
VNC (Virtual Network Computing)
VNC allows you to access the graphical desktop of your Raspberry Pi remotely. While not as secure as SSH, VNC can be configured with encryption to enhance security.
VPN (Virtual Private Network)
A VPN creates a secure tunnel between your device and Raspberry Pi, encrypting all traffic and protecting it from eavesdropping. This method is particularly useful for accessing resources on a private network.
Setting Up SSH for Secure Remote Access
SSH is a powerful tool for secure remote access on Raspberry Pi. By enabling SSH and configuring it properly, you can establish a secure connection to your device.
Steps to Enable SSH on Raspberry Pi
- Update your Raspberry Pi's operating system to ensure you have the latest security patches.
- Enable SSH by navigating to the Raspberry Pi Configuration menu and selecting the SSH option.
- Set up a strong password or use SSH keys for authentication to enhance security.
- Connect to your Raspberry Pi using an SSH client, such as PuTTY or Terminal.
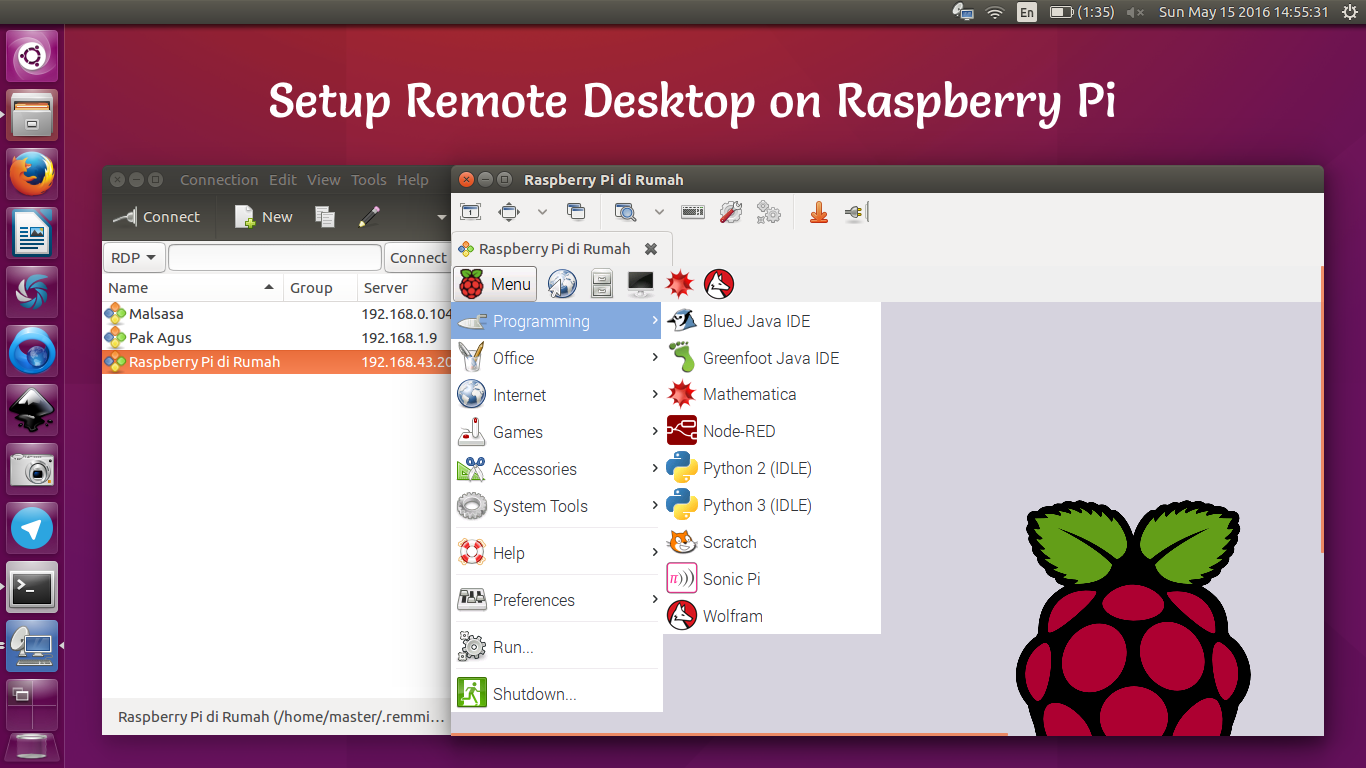
Using VNC for Remote Desktop Access
VNC provides a graphical interface for remote access, allowing you to interact with your Raspberry Pi as if you were sitting in front of it. While VNC is less secure than SSH, it can be configured with encryption to improve security.
Steps to Set Up VNC on Raspberry Pi
- Install the VNC Server software on your Raspberry Pi.
- Enable VNC by navigating to the Raspberry Pi Configuration menu and selecting the VNC option.
- Set up a secure password for VNC access and enable encryption if available.
- Connect to your Raspberry Pi using a VNC client, such as RealVNC Viewer or TightVNC.
Creating a Secure Tunnel with a Raspberry Pi VPN
A Raspberry Pi-based VPN can provide a secure tunnel for accessing your devices and networks remotely. By configuring a VPN on your Raspberry Pi, you can encrypt all traffic and protect it from unauthorized access.
Steps to Set Up a Raspberry Pi VPN
- Install a VPN server software, such as OpenVPN, on your Raspberry Pi.
- Configure the server settings to match your network requirements.
- Generate client certificates and keys for secure authentication.
- Connect to your Raspberry Pi VPN using a compatible client application.
Best Practices for Securing Your Raspberry Pi
Securing your Raspberry Pi is essential to ensure the safety of your remote access solution. Follow these best practices to enhance the security of your device:
- Keep Software Updated: Regularly update your Raspberry Pi's operating system and installed software to patch vulnerabilities.
- Use Strong Passwords: Set strong, unique passwords for all accounts and avoid using default credentials.
- Enable Firewall: Configure a firewall to restrict unauthorized access to your Raspberry Pi.
- Monitor Activity: Keep track of login attempts and system activity to detect suspicious behavior.
Troubleshooting Common Issues
While setting up secure remote access on Raspberry Pi is straightforward, you may encounter some issues along the way. Here are some common problems and their solutions:
- Connection Issues: Ensure that your Raspberry Pi is connected to the network and that the correct IP address is being used.
- Authentication Failures: Verify that your credentials are correct and that SSH or VNC is properly configured.
- Performance Problems: Optimize your Raspberry Pi's settings and ensure sufficient resources are available for remote access tasks.
Conclusion and Call to Action
Raspberry Pi secure remote access free solutions offer a powerful and cost-effective way to manage your devices remotely. By following the steps outlined in this guide, you can set up a secure and reliable remote access solution tailored to your needs.
We encourage you to explore the various methods and tools available for secure remote access on Raspberry Pi. Whether you choose SSH, VNC, or a Raspberry Pi-based VPN, each option provides unique benefits and can enhance your productivity and efficiency.
Don't forget to share your experiences and insights in the comments section below. Your feedback helps us improve and expand our content. Additionally, consider exploring other articles on our site to learn more about Raspberry Pi and its applications. Together, let's unlock the full potential of this remarkable device!