Securely Connect Remote IoT VPC: A Comprehensive Guide
Connecting remote IoT devices to a Virtual Private Cloud (VPC) securely is becoming increasingly important as organizations adopt more connected technologies. With the rise of IoT devices, ensuring secure communication between these devices and cloud environments has become a critical challenge. This article will explore the best practices and strategies to securely connect remote IoT VPC, helping you protect your data and network infrastructure.
As the number of IoT devices continues to grow exponentially, the demand for secure connectivity solutions rises alongside it. According to recent reports, the global IoT market is expected to reach $1.5 trillion by 2030. This rapid growth highlights the importance of implementing robust security measures to safeguard sensitive information and maintain system integrity.
This guide will provide you with actionable insights and expert advice to help you navigate the complexities of securely connecting remote IoT VPC. Whether you're a network administrator, IT professional, or business owner, this article will equip you with the knowledge needed to protect your IoT infrastructure effectively.
Read also:Securely Connect Remote Iot Vpc Raspberry Pi Download
Table of Contents
- Introduction to Secure IoT VPC Connections
- What is IoT VPC and Why Does It Matter?
- Security Challenges in IoT VPC
- Best Practices for Securely Connect Remote IoT VPC
- The Role of Encryption in IoT VPC Security
- Authentication Methods for IoT Devices
- Network Segmentation Strategies
- Implementing Firewalls for IoT VPC
- Monitoring and Threat Detection
- Compliance and Regulatory Considerations
- Conclusion and Next Steps
Introduction to Secure IoT VPC Connections
Securing IoT devices in a VPC environment is crucial for maintaining data privacy and network security. A Virtual Private Cloud (VPC) provides a dedicated and isolated environment for hosting cloud resources, ensuring that sensitive data remains protected from unauthorized access. This section will introduce the concept of securely connecting remote IoT VPC and explain why it is essential for modern businesses.
Organizations leveraging IoT technology must prioritize security to prevent potential breaches and ensure compliance with industry standards. By adopting a proactive approach to IoT VPC security, businesses can mitigate risks and protect their digital assets.
What is IoT VPC and Why Does It Matter?
An IoT VPC serves as a secure and scalable platform for managing IoT devices and applications. It allows businesses to deploy and manage IoT devices within a controlled environment, reducing the risk of unauthorized access and data breaches. Understanding the fundamentals of IoT VPC is essential for implementing effective security measures.
Key Features of IoT VPC
- Isolated network environment for IoT devices
- Scalable infrastructure to accommodate growing IoT deployments
- Advanced security features to protect sensitive data
By leveraging IoT VPC, organizations can streamline their IoT operations while ensuring compliance with security standards. This section will delve deeper into the benefits of IoT VPC and its role in modern network architectures.
Security Challenges in IoT VPC
Despite the advantages of IoT VPC, several security challenges must be addressed to ensure a secure connection between remote IoT devices and cloud environments. These challenges include:
- Unauthorized access to IoT devices
- Data interception and theft during transmission
- Malware and cyberattacks targeting IoT devices
Addressing these challenges requires a comprehensive security strategy that encompasses encryption, authentication, and network segmentation. This section will explore these challenges in detail and provide solutions to overcome them.
Read also:Who Is The Tallest Wwe Wrestler Unveiling The Giants Of The Ring
Best Practices for Securely Connect Remote IoT VPC
Implementing best practices for securely connecting remote IoT VPC is essential for maintaining data integrity and network security. These practices include:
1. Use Strong Encryption Protocols
Encryption ensures that data transmitted between IoT devices and cloud environments remains secure and unreadable to unauthorized parties. Protocols such as TLS and AES are widely used for securing IoT communications.
2. Implement Multi-Factor Authentication
Multi-factor authentication adds an extra layer of security by requiring users to provide multiple forms of verification before accessing IoT devices. This reduces the risk of unauthorized access and enhances overall security.
3. Regularly Update Firmware and Software
Keeping IoT devices and cloud environments up to date with the latest firmware and software patches helps address known vulnerabilities and strengthens security.
By following these best practices, organizations can significantly enhance the security of their IoT VPC infrastructure.
The Role of Encryption in IoT VPC Security
Encryption plays a critical role in securing IoT VPC connections by protecting sensitive data during transmission. It ensures that even if data is intercepted, it remains unreadable without the proper decryption key. This section will discuss the importance of encryption and the most commonly used encryption protocols in IoT VPC environments.
Types of Encryption Protocols
- TLS (Transport Layer Security)
- AES (Advanced Encryption Standard)
- SSL (Secure Sockets Layer)
Each protocol offers unique features and benefits, making them suitable for different use cases. By selecting the appropriate encryption protocol, organizations can ensure secure communication between IoT devices and cloud environments.
Authentication Methods for IoT Devices
Authentication is a fundamental aspect of IoT VPC security, ensuring that only authorized devices and users can access the network. This section will explore the various authentication methods available for IoT devices and their respective advantages.
Common Authentication Methods
- Username and Password
- Public Key Infrastructure (PKI)
- Biometric Authentication
Implementing robust authentication methods is essential for preventing unauthorized access and protecting sensitive data. Organizations should evaluate their security requirements and choose the most appropriate authentication method for their IoT VPC environment.
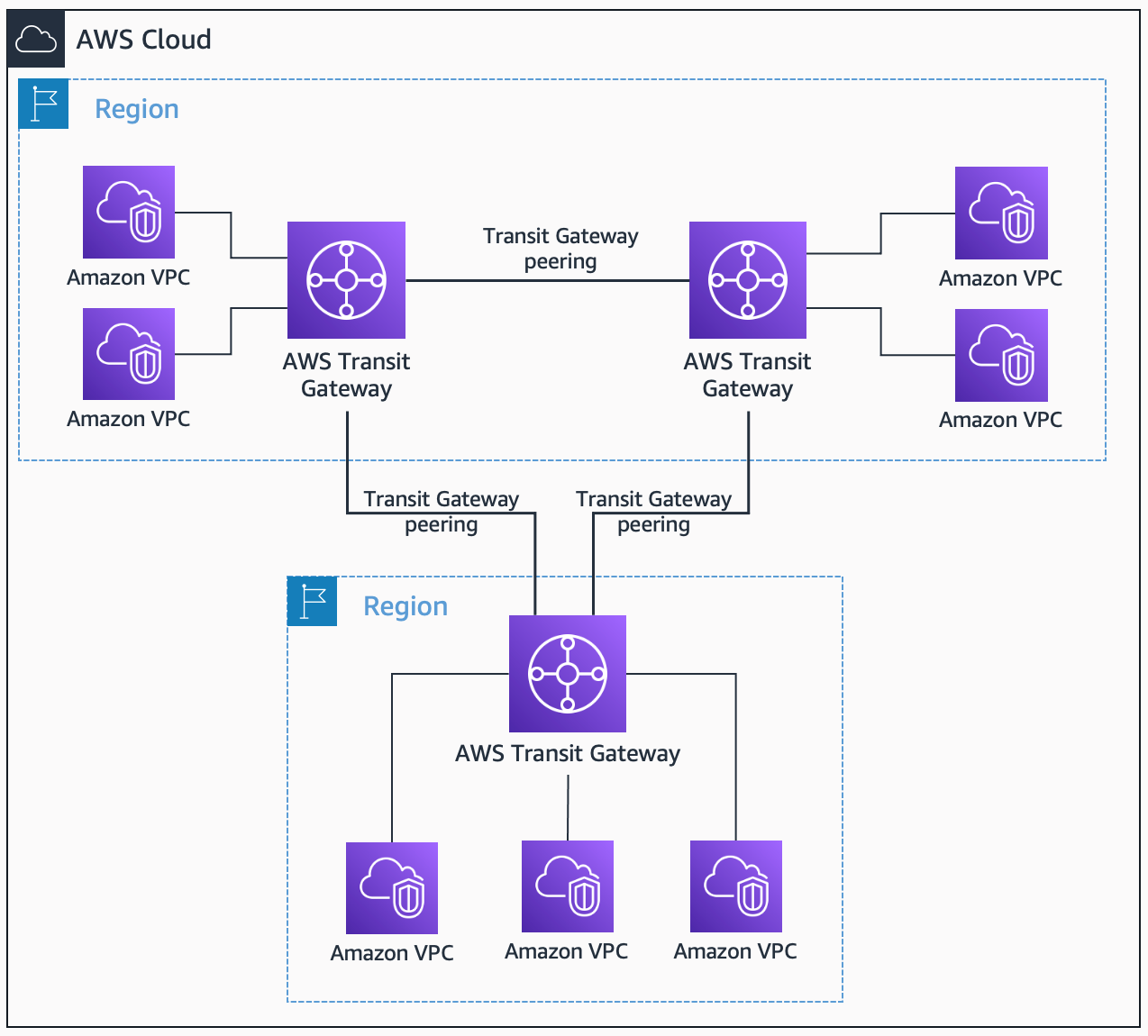
Network Segmentation Strategies
Network segmentation involves dividing a network into smaller, isolated segments to enhance security and improve performance. This strategy is particularly effective in IoT VPC environments, where sensitive data and critical systems must be protected from unauthorized access.
Benefits of Network Segmentation
- Reduced attack surface
- Improved network performance
- Enhanced security controls
By implementing network segmentation strategies, organizations can create a more secure and efficient IoT VPC environment. This section will provide practical guidance on designing and implementing effective network segmentation solutions.
Implementing Firewalls for IoT VPC
Firewalls serve as a critical line of defense in IoT VPC environments, blocking unauthorized access and filtering malicious traffic. This section will discuss the importance of firewalls in IoT VPC security and the various types of firewalls available.
Types of Firewalls
- Packet Filtering Firewalls
- Stateful Inspection Firewalls
- Next-Generation Firewalls
Selecting the right firewall for your IoT VPC environment depends on your specific security requirements and budget constraints. By implementing a robust firewall solution, organizations can significantly enhance the security of their IoT infrastructure.
Monitoring and Threat Detection
Continuous monitoring and threat detection are essential for maintaining the security of IoT VPC environments. This section will explore the tools and techniques used for monitoring IoT devices and detecting potential security threats.
Key Monitoring Tools
- Intrusion Detection Systems (IDS)
- Intrusion Prevention Systems (IPS)
- Security Information and Event Management (SIEM)
By leveraging these tools, organizations can proactively identify and respond to security threats, ensuring the integrity and availability of their IoT VPC infrastructure.
Compliance and Regulatory Considerations
Compliance with industry regulations and standards is crucial for organizations operating in IoT VPC environments. This section will discuss the key compliance requirements and how they impact IoT security.
Key Compliance Standards
- GDPR (General Data Protection Regulation)
- HIPAA (Health Insurance Portability and Accountability Act)
- ISO 27001
Organizations must ensure that their IoT VPC environments adhere to these standards to avoid potential legal and financial consequences. By implementing compliance measures, businesses can demonstrate their commitment to data protection and security.
Conclusion and Next Steps
Securing remote IoT VPC connections is a critical task for modern organizations seeking to leverage the benefits of IoT technology while maintaining data privacy and network security. By following the best practices outlined in this article, organizations can significantly enhance the security of their IoT infrastructure and protect against potential threats.
We encourage readers to take the following actions:
- Implement encryption and authentication protocols to secure IoT communications
- Adopt network segmentation strategies to isolate sensitive data and systems
- Regularly monitor and update IoT devices to address vulnerabilities
Feel free to share your thoughts and experiences in the comments section below. For more insights on IoT security and related topics, explore our other articles and resources. Together, we can build a safer and more secure digital future.