Securing Remote Access Raspberry Pi: A Comprehensive Guide
Securing remote access Raspberry Pi has become a critical need for tech enthusiasts and professionals alike. As more people leverage Raspberry Pi for remote operations, ensuring its security is paramount to protect sensitive data and maintain system integrity. Whether you're using Raspberry Pi for home automation, IoT projects, or server management, understanding the best practices for securing remote access is essential.
In this digital age, the popularity of Raspberry Pi continues to grow due to its versatility and affordability. However, with increased connectivity comes greater risks. This guide will walk you through the steps to secure your Raspberry Pi when enabling remote access, ensuring that your device remains protected against unauthorized access and potential cyber threats.
From configuring firewalls to implementing encryption protocols, we'll cover everything you need to know to safeguard your Raspberry Pi. Whether you're a beginner or an advanced user, this article provides actionable insights and expert tips to enhance the security of your remote access setup.
Read also:Movierulz 2023 Download Kannada Your Ultimate Guide To Movies
Table of Contents
- Introduction to Securing Remote Access Raspberry Pi
- Understanding the Basics of Raspberry Pi Security
- Configuring SSH for Secure Remote Access
- Setting Up a Firewall for Enhanced Protection
- Implementing Encryption Protocols
- Regularly Updating Your Raspberry Pi
- Strengthening Password Security
- Using VNC for Remote Desktop Access
- Securing Your Network Environment
- Best Practices for Securing Remote Access
- Conclusion
Introduction to Securing Remote Access Raspberry Pi
Securing remote access Raspberry Pi involves implementing multiple layers of security measures to protect your device from unauthorized access. As a versatile single-board computer, Raspberry Pi is often used in remote environments, making it a potential target for cybercriminals. To mitigate these risks, it's crucial to adopt a proactive approach to security.
Why Is Securing Remote Access Important?
Remote access to Raspberry Pi allows users to control and manage their devices from anywhere in the world. However, this convenience comes with risks. Without proper security measures, your Raspberry Pi could become vulnerable to attacks such as brute force, malware infections, and data breaches. Securing remote access ensures that only authorized users can interact with your device.
According to a report by Symantec, the number of IoT-related attacks has increased significantly in recent years. This underscores the importance of securing your Raspberry Pi, especially when it is connected to the internet.
Understanding the Basics of Raspberry Pi Security
Before diving into the specifics of securing remote access, it's essential to understand the fundamental aspects of Raspberry Pi security. This includes familiarizing yourself with the default settings, potential vulnerabilities, and best practices for securing your device.
Default Settings and Vulnerabilities
By default, Raspberry Pi comes with certain settings that may pose security risks if left unchanged. For example, the default username "pi" and password "raspberry" are widely known, making your device susceptible to unauthorized access. It's crucial to change these default credentials immediately after setting up your Raspberry Pi.
Additionally, Raspberry Pi's open-source nature means that vulnerabilities can be discovered and exploited by malicious actors. Staying informed about the latest security patches and updates is vital to maintaining a secure environment.
Read also:Who Is Hikaru Nagi A Comprehensive Guide To The Talented Japanese Musician
Configuring SSH for Secure Remote Access
SSH (Secure Shell) is one of the most common methods for enabling remote access to Raspberry Pi. It provides a secure channel for communication between your device and a remote client. Properly configuring SSH is essential to ensure the security of your remote access setup.
Steps to Configure SSH
- Enable SSH on your Raspberry Pi by running the command
sudo raspi-config. - Change the default SSH port from 22 to a custom port to reduce the risk of automated attacks.
- Disable password authentication and use SSH keys for added security.
- Limit SSH access to specific IP addresses or networks using the
/etc/hosts.allowfile.
By following these steps, you can significantly enhance the security of your SSH configuration and protect your Raspberry Pi from unauthorized access.
Setting Up a Firewall for Enhanced Protection
A firewall acts as a barrier between your Raspberry Pi and the internet, controlling incoming and outgoing traffic based on predefined rules. Setting up a firewall is an essential step in securing remote access to your device.
Using UFW for Firewall Management
UFW (Uncomplicated Firewall) is a user-friendly firewall management tool available on Raspberry Pi. To set up UFW, follow these steps:
- Install UFW by running the command
sudo apt-get install ufw. - Allow SSH access by running
sudo ufw allow ssh. - Enable the firewall with the command
sudo ufw enable. - Monitor and adjust firewall rules as needed to ensure optimal security.
By configuring UFW, you can effectively filter traffic and protect your Raspberry Pi from potential threats.
Implementing Encryption Protocols
Encryption plays a vital role in securing remote access to Raspberry Pi. By encrypting data transmitted between your device and remote clients, you can prevent unauthorized interception and ensure the confidentiality of your communications.
Using SSL/TLS for Encryption
SSL/TLS (Secure Sockets Layer/Transport Layer Security) is a widely used encryption protocol that can be implemented on Raspberry Pi to secure remote access. To enable SSL/TLS, you can use tools such as OpenSSL or configure your web server to use HTTPS.
Additionally, consider encrypting your SSH keys using a passphrase to add an extra layer of protection. This ensures that even if your private key is compromised, it cannot be used without the passphrase.
Regularly Updating Your Raspberry Pi
Keeping your Raspberry Pi up to date is crucial for maintaining security. Software updates often include important security patches that address known vulnerabilities. By regularly updating your device, you can protect it from potential threats.
Steps to Update Raspberry Pi
- Run the command
sudo apt-get updateto update the package list. - Run
sudo apt-get upgradeto install the latest software updates. - Reboot your Raspberry Pi to apply the updates using the command
sudo reboot.
Establishing a routine for updating your Raspberry Pi ensures that your device remains secure and performs optimally.
Strengthening Password Security
Weak passwords are one of the most common security vulnerabilities. To secure remote access to your Raspberry Pi, it's essential to implement strong password policies and consider alternative authentication methods.
Tips for Creating Strong Passwords
- Use a combination of uppercase and lowercase letters, numbers, and special characters.
- Avoid using easily guessable information such as names, birthdays, or common words.
- Make your passwords at least 12 characters long for added security.
Consider using password managers to generate and store complex passwords securely. Additionally, enabling two-factor authentication (2FA) adds an extra layer of protection by requiring a second form of verification.
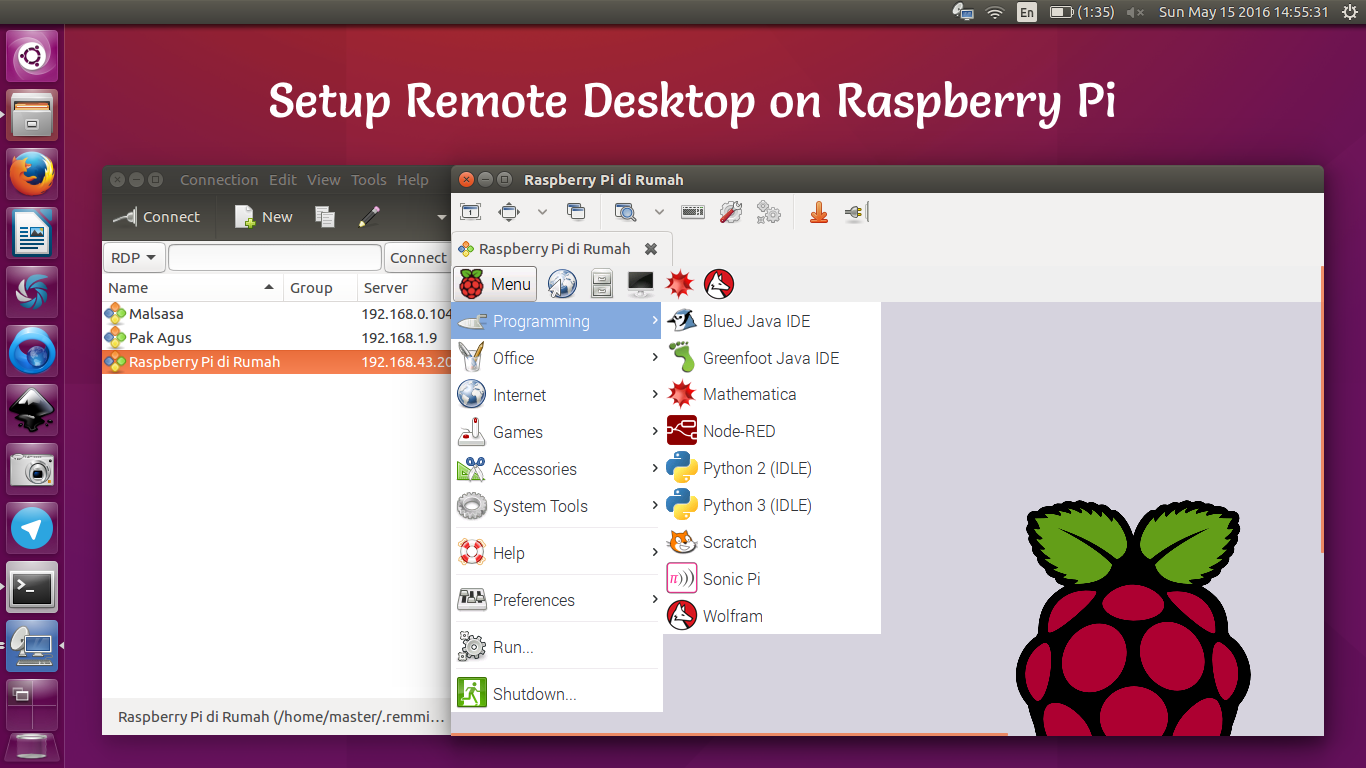
Using VNC for Remote Desktop Access
VNC (Virtual Network Computing) allows you to access the graphical desktop of your Raspberry Pi remotely. While convenient, VNC requires proper configuration to ensure secure remote access.
Configuring VNC for Security
- Install VNC Server on your Raspberry Pi by running
sudo apt-get install realvnc-vnc-server. - Set a strong password for VNC access and enable encryption.
- Limit VNC access to trusted networks or use a secure tunnel such as SSH.
By following these best practices, you can enjoy the benefits of remote desktop access while maintaining the security of your Raspberry Pi.
Securing Your Network Environment
Securing your Raspberry Pi involves not only configuring the device itself but also ensuring the security of your network environment. A secure network reduces the risk of unauthorized access and protects your device from external threats.
Network Security Best Practices
- Use a strong and unique password for your Wi-Fi network.
- Enable WPA3 encryption for wireless connections if supported by your router.
- Disable remote management features on your router unless absolutely necessary.
- Regularly monitor your network for suspicious activity and update router firmware.
By securing your network environment, you create a robust defense system that protects your Raspberry Pi and other connected devices.
Best Practices for Securing Remote Access
In addition to the specific measures discussed above, there are several best practices you can adopt to further enhance the security of your remote access setup for Raspberry Pi.
General Security Recommendations
- Limit the number of users with remote access privileges to your Raspberry Pi.
- Regularly audit your security settings and update them as needed.
- Backup your data regularly to prevent data loss in case of a security breach.
- Stay informed about the latest security trends and threats affecting Raspberry Pi.
By adhering to these best practices, you can maintain a secure and reliable remote access setup for your Raspberry Pi.
Conclusion
Securing remote access Raspberry Pi is a multifaceted process that requires a combination of technical skills and proactive security measures. By implementing SSH, configuring firewalls, enabling encryption, and following best practices, you can significantly enhance the security of your device.
We encourage you to take action and apply the tips and strategies outlined in this guide to protect your Raspberry Pi from potential threats. Share your thoughts and experiences in the comments below, and don't forget to explore our other articles for more valuable insights into technology and security.