Unlock The Power Of SSH Remote IoT Device Access For Free
In today's interconnected world, SSH remote IoT device access has become an essential tool for managing and monitoring smart devices from anywhere in the world. Whether you're a hobbyist, entrepreneur, or professional, understanding how to leverage free SSH solutions can significantly enhance your IoT projects' capabilities. This guide will walk you through everything you need to know about accessing IoT devices remotely using SSH without spending a dime.
As the Internet of Things (IoT) continues to expand, the demand for secure and efficient remote access solutions has never been higher. SSH (Secure Shell) provides a robust framework for managing devices remotely while maintaining data integrity and security. By exploring free SSH remote IoT device access options, you can unlock new possibilities for your projects without breaking the bank.
This comprehensive guide will cover everything from the basics of SSH to advanced configurations, ensuring you have all the tools needed to successfully implement remote access for your IoT devices. Whether you're a beginner or an experienced developer, this article will provide valuable insights and practical tips to enhance your IoT projects.
Read also:Comprehensive Guide To Movierulz 2025 Kannada Movie Download
Table of Contents
- Introduction to SSH Remote IoT Device Access
- Benefits of Using SSH for IoT Devices
- Exploring Free SSH Remote IoT Device Access Options
- The Setup Process for SSH Remote IoT Device Access
- Security Considerations for Free SSH Access
- Common Issues and Troubleshooting Tips
- Advanced Features for Enhanced Functionality
- Real-World Use Cases for SSH Remote IoT Device Access
- Comparison of Free SSH Solutions
- Future Trends in SSH Remote IoT Device Access
Introduction to SSH Remote IoT Device Access
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication between devices over an unsecured network. When it comes to IoT devices, SSH remote access provides a reliable way to manage and monitor these devices without being physically present. This section will cover the fundamental concepts of SSH and its application in IoT environments.
Why SSH Matters for IoT Devices
IoT devices often require frequent updates, troubleshooting, and monitoring. SSH remote access simplifies these tasks by providing a secure and efficient method for interacting with devices from anywhere in the world. By understanding the basics of SSH, you can take full advantage of its capabilities to enhance your IoT projects.
Key benefits of SSH for IoT devices include:
- Encrypted communication for enhanced security
- Command-line interface for efficient device management
- Support for file transfers and remote scripting
Benefits of Using SSH for IoT Devices
Implementing SSH remote IoT device access offers numerous advantages that make it a preferred choice for both beginners and professionals. In this section, we'll explore the top benefits of using SSH for managing IoT devices.
Enhanced Security
One of the primary advantages of SSH is its robust security features. By encrypting all data transmitted between devices, SSH ensures that sensitive information remains protected from unauthorized access. This is particularly important in IoT environments where security breaches can have significant consequences.
Cost-Effectiveness
Many SSH solutions are available for free, making it an affordable option for individuals and businesses looking to implement remote access capabilities without incurring significant costs. This section will highlight some of the best free SSH options available for IoT devices.
Read also:Top Tulsa Tax Expert Your Ultimate Guide To Expert Tax Services
Exploring Free SSH Remote IoT Device Access Options
Several platforms offer free SSH remote IoT device access solutions that cater to different needs and preferences. This section will provide an overview of some of the most popular options available today.
Ngrok
Ngrok is a widely-used tool that allows developers to create secure tunnels for accessing local servers and IoT devices remotely. With its free tier, Ngrok provides a simple and effective way to implement SSH remote access for IoT devices.
TunnelBear
TunnelBear offers a user-friendly interface for setting up SSH tunnels, making it an excellent choice for beginners. While primarily known for its VPN services, TunnelBear also supports SSH remote access, providing a versatile solution for IoT projects.
The Setup Process for SSH Remote IoT Device Access
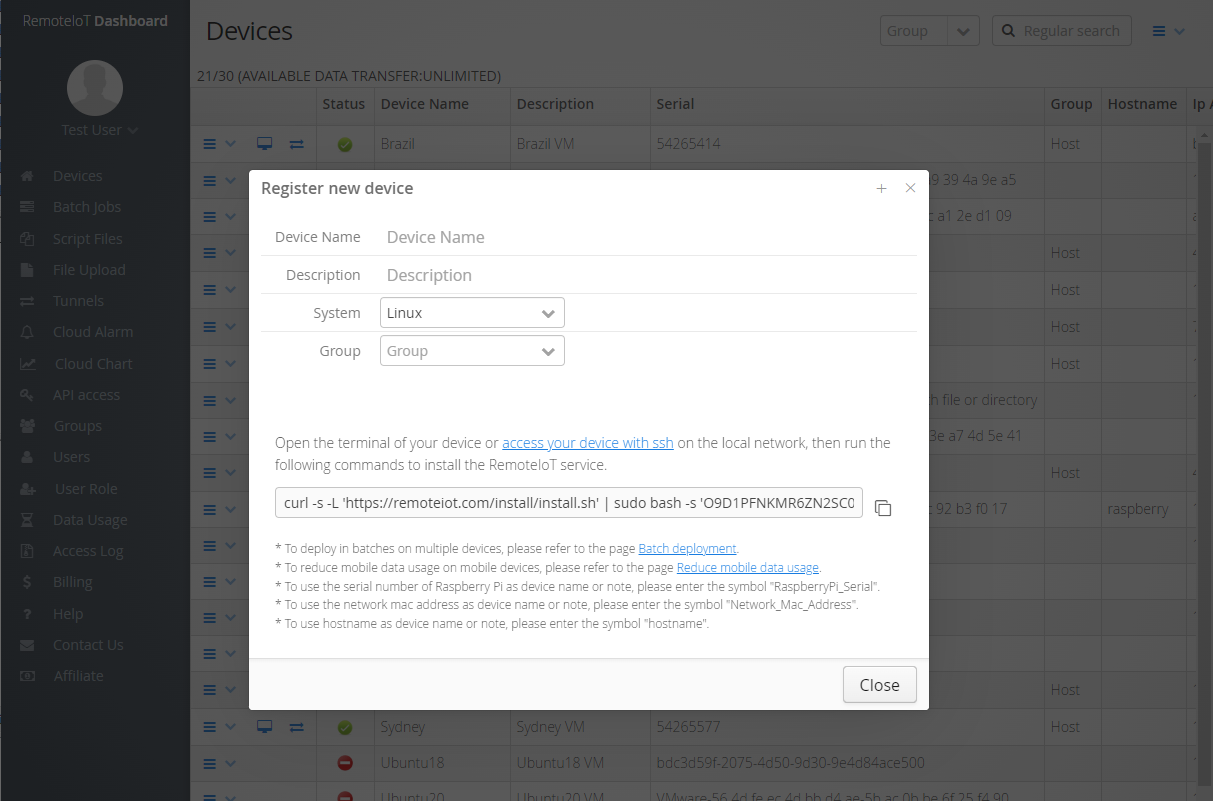
Setting up SSH remote IoT device access involves several steps that ensure secure and reliable communication between devices. This section will walk you through the entire process, from installing SSH on your IoT device to configuring remote access settings.
Step 1: Installing SSH on Your IoT Device
Before you can access your IoT device remotely, you need to install an SSH server on it. Most Linux-based IoT devices come with SSH pre-installed, but for others, you may need to install it manually. This section will provide detailed instructions for installing SSH on various IoT platforms.
Step 2: Configuring SSH Settings
Once SSH is installed, you'll need to configure its settings to ensure optimal performance and security. This includes setting up user accounts, configuring firewall rules, and enabling key-based authentication for added security.
Security Considerations for Free SSH Access
While SSH provides a secure method for remote access, it's essential to implement additional security measures to protect your IoT devices from potential threats. This section will discuss best practices for securing your SSH remote IoT device access setup.
Use Strong Passwords and Key-Based Authentication
One of the most effective ways to enhance SSH security is by using strong passwords and enabling key-based authentication. This section will explain how to generate SSH keys and configure your devices to use them for authentication.
Implement Firewall Rules
Configuring firewall rules can help prevent unauthorized access to your IoT devices. By restricting SSH access to specific IP addresses or networks, you can significantly reduce the risk of security breaches.
Common Issues and Troubleshooting Tips
Even with the best setup, issues can arise when implementing SSH remote IoT device access. This section will address common problems users may encounter and provide practical solutions to resolve them.
Connection Timeouts
Connection timeouts are a frequent issue when using SSH for remote access. This section will explore possible causes and provide troubleshooting steps to help you resolve the problem.
Authentication Failures
Authentication failures can occur due to incorrect passwords, expired keys, or misconfigured settings. By following the tips outlined in this section, you can quickly identify and fix the root cause of authentication issues.
Advanced Features for Enhanced Functionality
Once you've mastered the basics of SSH remote IoT device access, you can explore advanced features to further enhance your setup. This section will cover some of the most useful features available in SSH, including port forwarding, tunneling, and automation scripts.
Port Forwarding
Port forwarding allows you to access services running on your IoT device from outside your local network. This section will explain how to set up port forwarding using SSH and provide examples of common use cases.
Automation Scripts
Automating repetitive tasks using SSH scripts can save you time and effort. This section will provide examples of useful SSH scripts for managing IoT devices and offer tips for creating your own custom scripts.
Real-World Use Cases for SSH Remote IoT Device Access
To better understand the practical applications of SSH remote IoT device access, this section will explore real-world use cases across various industries. From smart home automation to industrial IoT applications, SSH provides a versatile solution for managing devices remotely.
Smart Home Automation
SSH remote access enables homeowners to monitor and control their smart home devices from anywhere in the world. This section will highlight some of the most popular smart home devices that support SSH and provide examples of how they can be managed remotely.
Industrial IoT Applications
In industrial settings, SSH remote IoT device access plays a crucial role in monitoring and maintaining critical infrastructure. This section will discuss how SSH is used in industries such as manufacturing, energy, and transportation to enhance operational efficiency and reduce downtime.
Comparison of Free SSH Solutions
With so many free SSH remote IoT device access options available, choosing the right solution can be challenging. This section will compare some of the most popular options based on features, ease of use, and security to help you make an informed decision.
Feature Comparison
By evaluating the features offered by different SSH solutions, you can determine which one best meets your needs. This section will provide a detailed comparison of key features such as encryption protocols, authentication methods, and platform support.
Security Comparison
Security is a top priority when implementing SSH remote access for IoT devices. This section will assess the security features of various SSH solutions and highlight any potential vulnerabilities to consider.
Future Trends in SSH Remote IoT Device Access
As the IoT landscape continues to evolve, new trends and technologies are emerging that will shape the future of SSH remote access. This section will explore upcoming developments in the field and discuss how they may impact SSH usage in IoT environments.
Quantum-Safe Encryption
With the advent of quantum computing, traditional encryption methods may become obsolete. This section will examine how SSH is adapting to this challenge by incorporating quantum-safe encryption protocols.
Edge Computing Integration
Edge computing is revolutionizing the way IoT devices process and transmit data. This section will explore how SSH remote access is being integrated with edge computing technologies to enhance performance and security.
Kesimpulan
In conclusion, SSH remote IoT device access offers a secure and cost-effective solution for managing and monitoring smart devices from anywhere in the world. By understanding the fundamentals of SSH and exploring the various free options available, you can unlock new possibilities for your IoT projects without incurring significant costs.
We encourage you to take action by experimenting with the tools and techniques discussed in this guide. Share your experiences in the comments section below and explore other articles on our site to deepen your knowledge of IoT and related technologies. Together, we can continue to advance the field of IoT and create a smarter, more connected world.
References:
- https://www.ssh.com/ssh
- https://ngrok.com/
- https://tunnelbear.com/