Best Remote IoT Firewall Examples: Enhancing Network Security
As technology continues to evolve, the Internet of Things (IoT) has become an integral part of modern life. However, with the increasing number of connected devices, ensuring network security has become more critical than ever. Remote IoT firewalls play a pivotal role in safeguarding your devices and data from cyber threats. This article will explore the best remote IoT firewall examples and provide actionable insights into how you can protect your IoT infrastructure.
In today's hyper-connected world, the importance of securing IoT devices cannot be overstated. Cyberattacks targeting IoT networks are on the rise, making it essential for individuals and organizations to adopt robust security measures. A remote IoT firewall is one such measure that acts as a digital shield, filtering malicious traffic and unauthorized access.
This article aims to provide comprehensive guidance on selecting the best remote IoT firewall solutions. Whether you're a tech enthusiast or a business owner, understanding the capabilities of these firewalls can significantly enhance your cybersecurity posture. Let's dive into the details and uncover the top remote IoT firewall examples that are reshaping the security landscape.
Read also:Can You Have A Cosigner For A Usda Loan
Table of Contents
- Introduction to Remote IoT Firewalls
- Biography of Remote IoT Firewalls
- Types of Remote IoT Firewalls
- Best Remote IoT Firewall Examples
- How to Implement Remote IoT Firewalls
- Benefits of Using Remote IoT Firewalls
- Comparison of Remote IoT Firewalls
- Security Features of Remote IoT Firewalls
- Cost Considerations for Remote IoT Firewalls
- Future Trends in Remote IoT Firewalls
Introduction to Remote IoT Firewalls
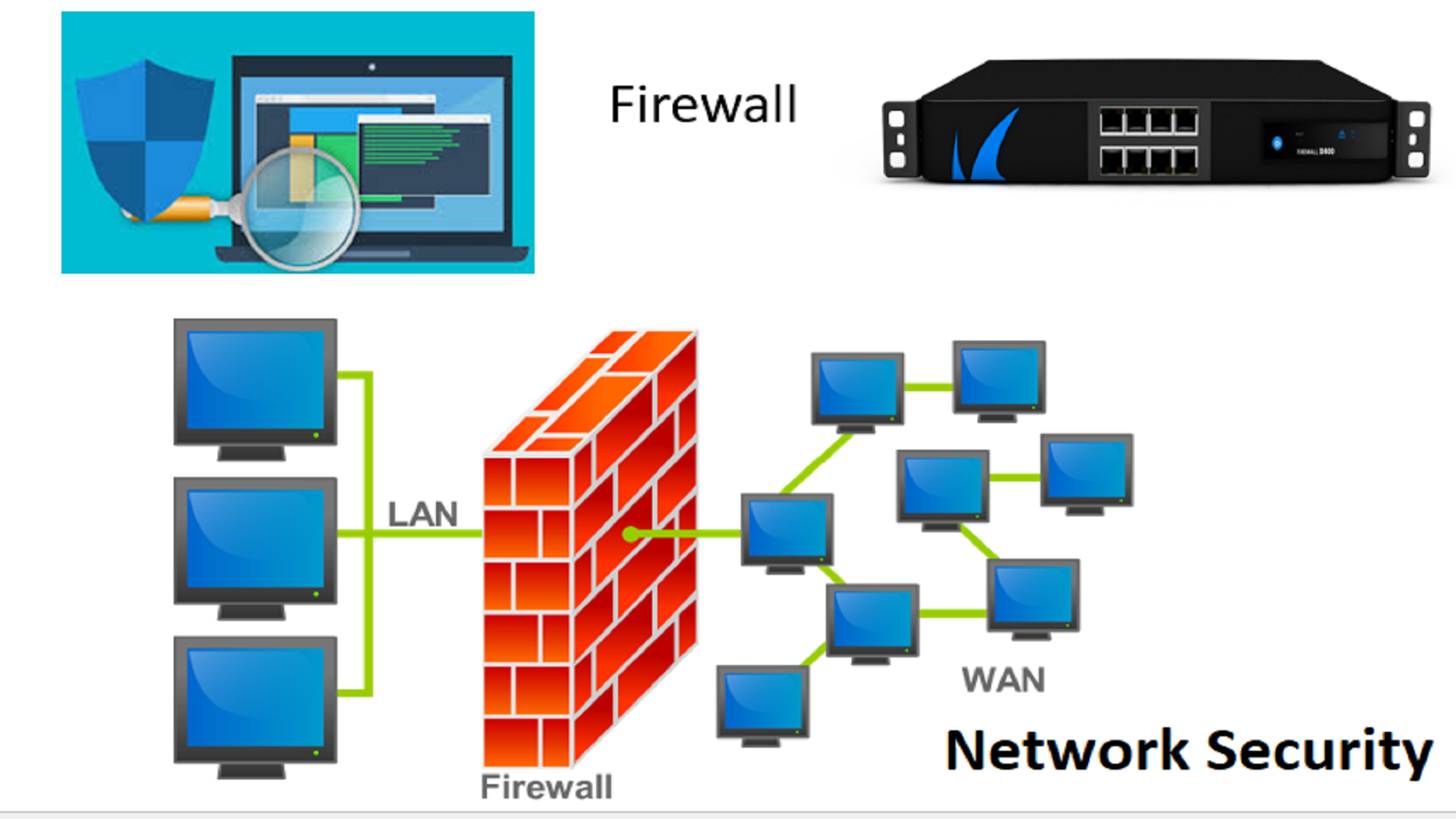
A remote IoT firewall is a specialized security solution designed to protect IoT devices and networks from cyber threats. Unlike traditional firewalls, remote IoT firewalls focus specifically on the unique challenges posed by IoT devices, such as limited processing power and diverse communication protocols.
As IoT adoption grows, so does the need for effective security measures. Remote IoT firewalls provide a layer of protection by monitoring and controlling incoming and outgoing network traffic based on predetermined security rules. This ensures that only legitimate traffic is allowed to pass through, reducing the risk of unauthorized access and data breaches.
Key features of remote IoT firewalls include real-time threat detection, advanced filtering capabilities, and seamless integration with existing network infrastructure. By implementing a remote IoT firewall, you can significantly enhance the security of your IoT ecosystem.
Biography of Remote IoT Firewalls
History and Development
The concept of firewalls dates back to the early days of computer networking. However, the rise of IoT devices has necessitated the development of specialized firewalls tailored to their unique requirements. Remote IoT firewalls have evolved to address the specific challenges of securing IoT networks, such as managing large numbers of devices and ensuring compatibility with various protocols.
Data and Biodata
| Parameter | Details |
|---|---|
| First Development | Mid-2000s |
| Primary Purpose | Securing IoT Networks |
| Key Innovators | Companies like Palo Alto Networks, Fortinet, and Check Point |
| Current Status | Rapidly Evolving with AI and Machine Learning Integration |
Types of Remote IoT Firewalls
Remote IoT firewalls come in various forms, each catering to different security needs and use cases. The main types include:
- Hardware-Based Firewalls: Physical devices installed at the network perimeter to provide dedicated security.
- Software-Based Firewalls: Applications installed on IoT devices or servers to filter network traffic.
- Cloud-Based Firewalls: Centralized security solutions hosted in the cloud, offering scalability and ease of management.
Selecting the right type of firewall depends on factors such as budget, network size, and specific security requirements.
Read also:Discover The Allure Of Rata Mexicana A Cultural And Culinary Journey
Best Remote IoT Firewall Examples
1. Palo Alto Networks
Palo Alto Networks offers cutting-edge remote IoT firewalls that combine advanced threat detection with comprehensive network visibility. Their solutions leverage machine learning to identify and mitigate potential threats in real time.
2. Fortinet FortiGate
FortiGate is a popular choice for organizations seeking robust security for their IoT networks. It provides a wide range of features, including intrusion prevention, application control, and secure access.
3. Check Point IoT Security
Check Point's IoT Security solution is designed to protect IoT devices from cyberattacks by offering advanced threat prevention capabilities. It integrates seamlessly with existing network infrastructure, making it an ideal choice for businesses of all sizes.
How to Implement Remote IoT Firewalls
Implementing a remote IoT firewall involves several key steps:
- Assess Your Network: Identify the IoT devices and network components that require protection.
- Select the Right Solution: Choose a firewall that aligns with your security needs and budget.
- Configure Security Rules: Set up rules and policies to control network traffic and block malicious activity.
- Monitor and Update: Regularly monitor firewall performance and update security settings to address emerging threats.
By following these steps, you can ensure that your IoT network remains secure and protected against potential threats.
Benefits of Using Remote IoT Firewalls
Remote IoT firewalls offer numerous benefits, including:
- Enhanced Security: Protects IoT devices and networks from unauthorized access and cyberattacks.
- Improved Network Performance: Filters out unnecessary traffic, ensuring optimal network performance.
- Centralized Management: Simplifies security management by providing a single interface for monitoring and control.
- Cost-Effectiveness: Reduces the risk of costly data breaches and downtime caused by cyberattacks.
These benefits make remote IoT firewalls an essential component of any comprehensive cybersecurity strategy.
Comparison of Remote IoT Firewalls
When comparing remote IoT firewalls, it's essential to consider factors such as performance, scalability, and ease of use. Below is a comparison of some leading solutions:
| Firewall | Performance | Scalability | Ease of Use |
|---|---|---|---|
| Palo Alto Networks | Excellent | High | Advanced |
| Fortinet FortiGate | Very Good | Medium | Good |
| Check Point IoT Security | Good | Medium | Easy |
Security Features of Remote IoT Firewalls
Modern remote IoT firewalls come equipped with a variety of advanced security features, including:
- Real-Time Threat Detection: Identifies and blocks malicious traffic in real time.
- Intrusion Prevention System (IPS): Prevents unauthorized access and potential breaches.
- Application Control: Monitors and manages application usage to ensure compliance with security policies.
- Encryption: Protects data in transit by encrypting sensitive information.
These features collectively enhance the security of IoT networks, making them more resilient to cyber threats.
Cost Considerations for Remote IoT Firewalls
The cost of implementing a remote IoT firewall varies depending on factors such as the type of firewall, the number of devices to be protected, and the level of support required. On average, hardware-based firewalls tend to be more expensive upfront but offer better performance, while software-based solutions are more cost-effective but may require additional resources for management.
Cloud-based firewalls often operate on a subscription model, providing flexibility and scalability without the need for significant upfront investment. When evaluating costs, it's important to consider both initial expenses and long-term maintenance requirements.
Future Trends in Remote IoT Firewalls
The future of remote IoT firewalls looks promising, with advancements in AI and machine learning driving innovation in this field. Key trends to watch include:
- AI-Driven Threat Detection: Enhanced threat detection capabilities powered by artificial intelligence.
- Zero-Trust Architecture: Adoption of zero-trust principles to ensure secure access to IoT devices and networks.
- Integration with Other Security Solutions: Seamless integration with other security tools and platforms for comprehensive protection.
As technology continues to evolve, remote IoT firewalls will play an increasingly important role in safeguarding IoT networks and devices.
Kesimpulan
Remote IoT firewalls are essential tools for securing IoT networks and protecting against cyber threats. By selecting the right solution and implementing best practices, you can significantly enhance the security of your IoT infrastructure. Whether you choose a hardware-based, software-based, or cloud-based firewall, the key is to ensure that it meets your specific security needs and integrates seamlessly with your existing network.
We encourage you to share your thoughts and experiences with remote IoT firewalls in the comments below. Additionally, feel free to explore other articles on our website for more insights into cybersecurity and IoT security. Together, let's build a safer digital future!
Sources:
- Palo Alto Networks - https://www.paloaltonetworks.com/
- Fortinet - https://www.fortinet.com/
- Check Point - https://www.checkpoint.com/