Mastering RemoteIoT VPC SSH: A Comprehensive Guide
RemoteIoT VPC SSH has become a crucial component for managing secure and efficient IoT deployments in cloud environments. As more businesses adopt IoT technologies, understanding how to configure and secure Virtual Private Cloud (VPC) environments using SSH is essential. This guide will walk you through everything you need to know about RemoteIoT VPC SSH, from its basics to advanced configurations, ensuring your IoT infrastructure remains robust and secure.
In today's interconnected world, IoT devices are increasingly deployed across various industries, from healthcare to manufacturing. However, managing these devices securely is a challenge. This is where RemoteIoT VPC SSH comes into play, providing a secure tunnel for accessing and managing IoT devices within a cloud-based VPC environment.
Whether you're a developer, network administrator, or IT professional, this article will equip you with the knowledge and tools needed to implement and manage RemoteIoT VPC SSH effectively. Let's dive in and explore the world of secure IoT management.
Read also:Kannada Blue Film A Comprehensive Guide To Understanding The Controversial Industry
Table of Contents
- Introduction to RemoteIoT VPC SSH
- Understanding the Architecture
- Setting Up RemoteIoT VPC SSH
- Enhancing Security Measures
- Common Issues and Troubleshooting
- Optimizing Performance
- Scaling Your IoT Infrastructure
- Monitoring and Maintenance
- Best Practices for RemoteIoT VPC SSH
- The Future of RemoteIoT VPC SSH
Introduction to RemoteIoT VPC SSH
What is RemoteIoT VPC SSH?
RemoteIoT VPC SSH refers to the use of Secure Shell (SSH) protocols to manage IoT devices within a Virtual Private Cloud (VPC) environment. This setup allows administrators to securely connect to IoT devices over the internet without exposing them to public networks, reducing security risks.
SSH provides encryption for data transmission, ensuring that sensitive information remains protected during communication between the administrator and IoT devices. By integrating SSH with VPC, organizations can create isolated networks for their IoT deployments, enhancing both security and performance.
Why Use RemoteIoT VPC SSH?
There are several reasons why RemoteIoT VPC SSH is preferred by organizations:
- Enhanced Security: Protects against unauthorized access and data breaches.
- Scalability: Easily scale IoT deployments without compromising security.
- Efficient Management: Centralized control over IoT devices within a VPC environment.
- Cost-Effective: Reduces the need for on-premises infrastructure, lowering operational costs.
Understanding the Architecture
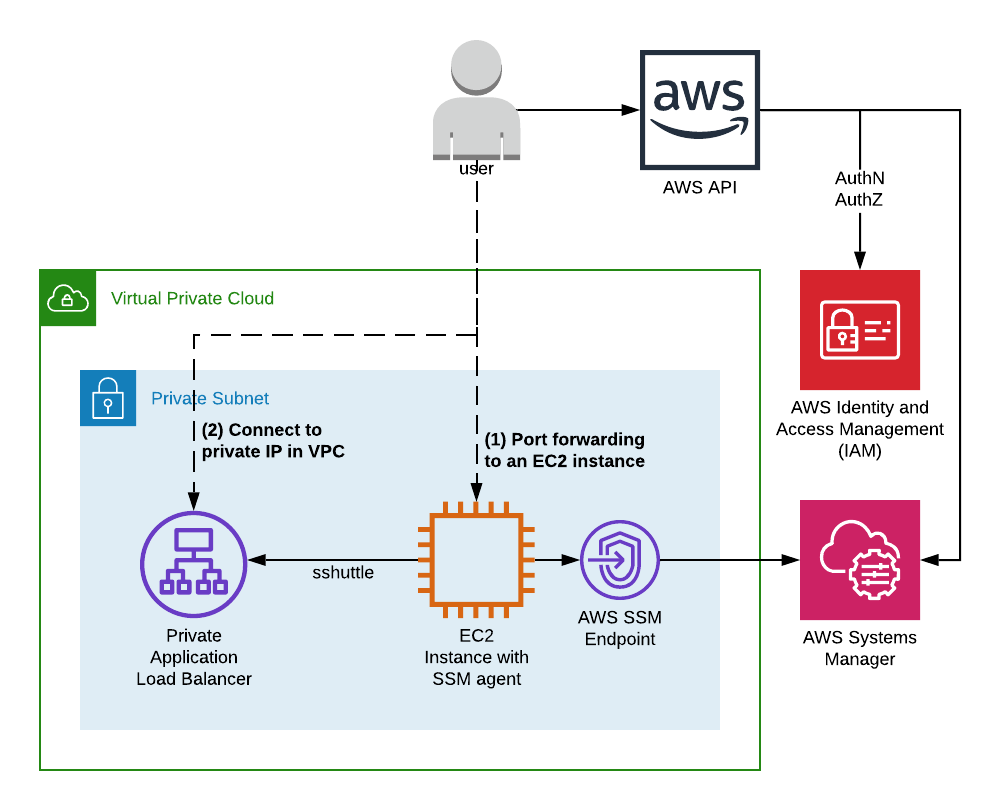
Before implementing RemoteIoT VPC SSH, it's essential to understand its architecture. The architecture typically consists of the following components:
Key Components
- VPC Network: A virtual network dedicated to your AWS resources, providing a secure and isolated environment for IoT devices.
- SSH Server: A server running on an IoT device or gateway, allowing secure connections via SSH.
- SSH Client: A tool used by administrators to connect to the SSH server, typically installed on their local machines.
- Security Groups: Define inbound and outbound traffic rules for your VPC, ensuring only authorized connections are allowed.
Setting Up RemoteIoT VPC SSH
Step-by-Step Guide
Setting up RemoteIoT VPC SSH involves several steps:
- Create a VPC: Use AWS Management Console to create a VPC tailored to your IoT deployment needs.
- Launch an EC2 Instance: Deploy an EC2 instance within the VPC to act as a gateway for your IoT devices.
- Install SSH Server: Configure the EC2 instance with an SSH server, such as OpenSSH.
- Configure Security Groups: Set up security groups to allow SSH traffic (port 22) from trusted IP addresses.
- Test the Connection: Use an SSH client to connect to the EC2 instance and verify the setup.
Enhancing Security Measures
Best Security Practices
Security is paramount when managing IoT devices. Here are some best practices to enhance security:
Read also:Kash Patel Eye Injury Update Latest Developments And Insights
- Use strong, unique passwords or SSH keys for authentication.
- Disable password-based authentication and rely solely on SSH keys.
- Regularly update SSH server software to patch vulnerabilities.
- Monitor and analyze logs for suspicious activities.
Implementing Firewall Rules
Firewall rules play a crucial role in securing your VPC environment. By defining strict rules, you can limit access to only necessary services and IP addresses.
Common Issues and Troubleshooting
Troubleshooting Tips
Despite careful setup, issues may arise. Here are some common problems and their solutions:
- Connection Refused: Check security group settings and ensure SSH port (22) is open.
- Authentication Failed: Verify SSH keys or passwords and ensure they match.
- Timeout Errors: Investigate network connectivity and ensure no firewalls block SSH traffic.
Optimizing Performance
Improving SSH Performance
To optimize the performance of RemoteIoT VPC SSH, consider the following:
- Use compression to reduce data transfer sizes.
- Enable keepalive settings to maintain persistent connections.
- Optimize server configurations for better resource utilization.
Scaling Your IoT Infrastructure
Scaling Strategies
As your IoT deployment grows, scaling becomes necessary. Here are some strategies to consider:
- Use auto-scaling groups to dynamically adjust resources based on demand.
- Implement load balancers to distribute traffic evenly across instances.
- Utilize AWS IoT Core for managing large-scale IoT fleets.
Monitoring and Maintenance
Monitoring Tools
Effective monitoring ensures your RemoteIoT VPC SSH remains healthy and secure. Tools like AWS CloudWatch and third-party solutions can help:
- Monitor system metrics such as CPU usage and network traffic.
- Set up alerts for unusual activities or performance degradation.
- Track changes to security group rules and configurations.
Best Practices for RemoteIoT VPC SSH
Adopting Best Practices
Following best practices ensures a secure and efficient RemoteIoT VPC SSH setup:
- Regularly review and update security policies.
- Perform routine backups of critical data.
- Train staff on secure SSH practices and protocols.
The Future of RemoteIoT VPC SSH
As IoT technology continues to evolve, so does the role of RemoteIoT VPC SSH. Future advancements may include:
- Enhanced encryption algorithms for stronger security.
- Integration with AI and machine learning for predictive maintenance.
- Improved automation tools for easier management and scaling.
Conclusion
In conclusion, RemoteIoT VPC SSH is a powerful tool for managing IoT deployments securely and efficiently. By understanding its architecture, implementing best practices, and staying updated with the latest advancements, you can ensure your IoT infrastructure remains robust and secure.
We encourage you to share your thoughts and experiences in the comments below. Additionally, explore other articles on our site to deepen your knowledge of IoT and cloud technologies. Together, let's build a safer and more connected future!
Data Source: AWS IoT Core, OpenSSH