Best RemoteIoT Web SSH: Your Ultimate Guide To Secure Remote Access
In today's interconnected world, the need for secure and efficient remote access solutions has become more critical than ever. Best RemoteIoT Web SSH offers a robust solution for managing IoT devices and servers remotely, ensuring seamless connectivity and data security. As businesses increasingly adopt IoT technologies, understanding and implementing secure remote access protocols is essential for maintaining operational efficiency.
RemoteIoT Web SSH provides a secure channel for connecting to IoT devices and servers from anywhere in the world. With advancements in technology, the ability to manage and monitor systems remotely has become indispensable for businesses of all sizes. This article delves into the intricacies of RemoteIoT Web SSH, exploring its features, benefits, and implementation strategies.
Whether you're a tech enthusiast, a network administrator, or a business owner looking to enhance your remote access capabilities, this guide will provide valuable insights into leveraging RemoteIoT Web SSH for secure and efficient operations. Let's explore how this technology can revolutionize the way you manage your IoT infrastructure.
Read also:The Worst Careers For Virgos A Comprehensive Guide
Table of Contents
- Introduction to RemoteIoT Web SSH
- Key Features of RemoteIoT Web SSH
- Benefits of Using RemoteIoT Web SSH
- How Does RemoteIoT Web SSH Work?
- Security Considerations
- Comparison with Other Remote Access Solutions
- Best Practices for Implementation
- Use Cases and Applications
- Common Questions About RemoteIoT Web SSH
- Conclusion and Next Steps
Introduction to RemoteIoT Web SSH
RemoteIoT Web SSH is a cutting-edge solution designed to facilitate secure remote access to IoT devices and servers. This technology leverages the power of SSH (Secure Shell) to create an encrypted connection between devices, ensuring data integrity and confidentiality. The growing demand for remote management capabilities has driven the development of solutions like RemoteIoT Web SSH, which cater to the needs of modern businesses.
What is SSH and Why is it Important?
SSH, or Secure Shell, is a network protocol that provides secure communication over unsecured networks. It is widely used for remote command-line login and execution, file transfer, and tunneling. The importance of SSH lies in its ability to encrypt data, authenticate users, and protect against unauthorized access. RemoteIoT Web SSH builds upon these core functionalities to deliver a comprehensive remote access solution.
Advancements in IoT and Their Impact on Remote Access
The Internet of Things (IoT) has revolutionized the way devices interact and communicate. With billions of connected devices worldwide, the need for efficient remote access solutions has never been greater. RemoteIoT Web SSH addresses this need by offering a scalable and secure platform for managing IoT infrastructure.
Key Features of RemoteIoT Web SSH
RemoteIoT Web SSH is equipped with a range of features that make it a top choice for remote access solutions. Below are some of its standout features:
- End-to-End Encryption: Ensures data security by encrypting all communication between devices.
- Multi-Platform Support: Compatible with various operating systems, including Windows, macOS, and Linux.
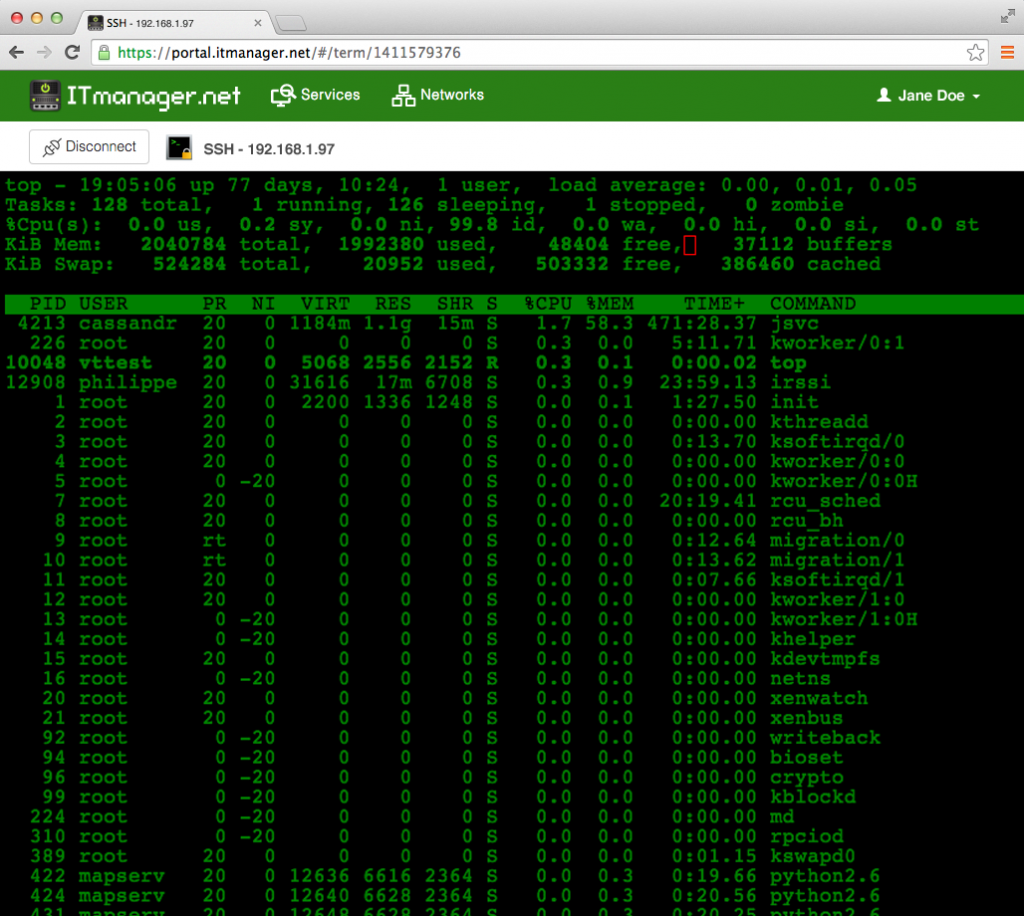
- Web-Based Interface: Provides an intuitive and user-friendly interface for managing devices remotely.
- Automated Updates: Ensures devices are always up-to-date with the latest security patches and features.
Advanced Authentication Mechanisms
RemoteIoT Web SSH incorporates advanced authentication methods, such as two-factor authentication (2FA) and public key authentication, to enhance security. These mechanisms ensure that only authorized users can access sensitive systems and data.
Benefits of Using RemoteIoT Web SSH
Adopting RemoteIoT Web SSH offers numerous benefits for businesses and individuals alike. Some of the key advantages include:
Read also:Hornysimp Understanding The Trend And Its Cultural Impact
- Improved Security: Protects against unauthorized access and cyber threats through robust encryption and authentication protocols.
- Increased Efficiency: Enables seamless management of IoT devices and servers from anywhere in the world.
- Cost Savings: Reduces the need for on-site maintenance, resulting in significant cost savings.
- Scalability: Supports a growing number of devices and users, making it ideal for businesses of all sizes.
Enhancing Business Operations
By integrating RemoteIoT Web SSH into their operations, businesses can improve productivity, reduce downtime, and enhance overall efficiency. The ability to monitor and manage devices remotely allows for quicker response times and better decision-making.
How Does RemoteIoT Web SSH Work?
RemoteIoT Web SSH operates by establishing a secure connection between a client and a server using the SSH protocol. The process involves several steps, including authentication, encryption, and data transmission. Below is a simplified overview of how RemoteIoT Web SSH works:
- Connection Initiation: The client initiates a connection to the server using the SSH protocol.
- Authentication: The server verifies the identity of the client using authentication methods such as passwords or public keys.
- Encryption: Data is encrypted before being transmitted between the client and server, ensuring confidentiality.
- Data Transmission: Encrypted data is sent over the network, maintaining security and integrity throughout the session.
Understanding the SSH Protocol
The SSH protocol is a fundamental component of RemoteIoT Web SSH. It provides a secure channel for communication by encrypting data and authenticating users. Understanding the inner workings of SSH is essential for maximizing the benefits of RemoteIoT Web SSH.
Security Considerations
While RemoteIoT Web SSH offers robust security features, it is important to adhere to best practices to ensure maximum protection. Below are some security considerations to keep in mind:
- Regular Software Updates: Keep all software and firmware up-to-date to address security vulnerabilities.
- Strong Passwords: Use complex passwords and enable two-factor authentication for added security.
- Network Segmentation: Isolate critical systems from less secure networks to minimize risk.
- Access Control: Limit access to sensitive systems and data to authorized personnel only.
Addressing Common Security Threats
RemoteIoT Web SSH helps mitigate common security threats such as unauthorized access, data breaches, and malware attacks. By implementing strong security measures, businesses can protect their IoT infrastructure and ensure uninterrupted operations.
Comparison with Other Remote Access Solutions
RemoteIoT Web SSH stands out from other remote access solutions due to its focus on security, scalability, and ease of use. Below is a comparison of RemoteIoT Web SSH with popular alternatives:
| Feature | RemoteIoT Web SSH | Alternative 1 | Alternative 2 |
|---|---|---|---|
| Encryption | End-to-End | Basic | Limited |
| Authentication | Advanced | Standard | Basic |
| Scalability | High | Moderate | Low |
Why Choose RemoteIoT Web SSH?
RemoteIoT Web SSH offers a superior combination of security, performance, and user experience, making it the preferred choice for businesses seeking a reliable remote access solution.
Best Practices for Implementation
Successfully implementing RemoteIoT Web SSH requires careful planning and execution. Below are some best practices to follow:
- Conduct a Needs Assessment: Identify the specific requirements of your organization to tailor the implementation accordingly.
- Plan the Deployment: Develop a detailed deployment plan, including timelines, resources, and responsibilities.
- Train Staff: Provide training to ensure staff members are familiar with the system and its features.
- Monitor Performance: Regularly monitor system performance to identify and address any issues promptly.
Ensuring a Smooth Transition
A well-planned implementation ensures a smooth transition to RemoteIoT Web SSH, minimizing disruption to business operations. By following best practices, organizations can maximize the benefits of this powerful solution.
Use Cases and Applications
RemoteIoT Web SSH finds applications in various industries and use cases. Below are some examples:
- Industrial Automation: Manage and monitor IoT devices in manufacturing plants and warehouses.
- Healthcare: Securely access medical devices and systems for remote diagnostics and monitoring.
- Smart Cities: Control and manage infrastructure such as traffic lights, streetlights, and public transportation systems.
Real-World Applications
Organizations across the globe have successfully implemented RemoteIoT Web SSH to enhance their remote access capabilities. These real-world applications demonstrate the versatility and effectiveness of the solution.
Common Questions About RemoteIoT Web SSH
Below are answers to some frequently asked questions about RemoteIoT Web SSH:
- Q: Is RemoteIoT Web SSH easy to use? A: Yes, it features an intuitive web-based interface that simplifies remote management tasks.
- Q: Can it be integrated with existing systems? A: Absolutely, RemoteIoT Web SSH is designed to seamlessly integrate with existing infrastructure.
- Q: What support options are available? A: Comprehensive support options, including documentation, tutorials, and customer support, are provided.
Addressing Common Concerns
Understanding common concerns and providing clear answers helps build trust and confidence in RemoteIoT Web SSH as a reliable solution.
Conclusion and Next Steps
In conclusion, RemoteIoT Web SSH offers a secure, scalable, and efficient solution for managing IoT devices and servers remotely. Its advanced features, robust security measures, and ease of use make it an ideal choice for businesses looking to enhance their remote access capabilities. By adopting RemoteIoT Web SSH, organizations can improve productivity, reduce costs, and ensure the security of their IoT infrastructure.
Take the next step by exploring how RemoteIoT Web SSH can benefit your organization. Leave a comment below or share this article with others who may find it valuable. For more information, check out our other articles on IoT and remote access solutions.
References: