Comprehensive RemoteIoT Device SSH Tutorial For Beginners
RemoteIoT devices have revolutionized the way we interact with technology across various industries, from smart homes to industrial automation. Understanding how to securely connect to these devices using SSH (Secure Shell) is crucial for managing and maintaining them effectively. In this tutorial, we will guide you step-by-step through the process of setting up and accessing remote IoT devices via SSH.
As more organizations adopt IoT solutions, the demand for secure communication protocols increases. SSH provides an encrypted channel between devices, ensuring data privacy and security. Whether you're a beginner or an experienced IT professional, mastering SSH for IoT devices is essential for maintaining robust networks.
This article will walk you through everything you need to know about RemoteIoT devices and SSH, including setup instructions, troubleshooting tips, and best practices. By the end of this tutorial, you'll be equipped with the knowledge to securely manage your IoT infrastructure.
Read also:Download Movierulzcom App Your Ultimate Guide To Accessing Movies Anywhere
Table of Contents
- Introduction to RemoteIoT Devices
- What is SSH?
- Setting Up a RemoteIoT Device
- Connecting to a RemoteIoT Device via SSH
- Securing SSH Connections
- Troubleshooting Common Issues
- Advanced SSH Configurations
- Best Practices for RemoteIoT SSH Management
- Use Cases for RemoteIoT SSH
- Conclusion and Next Steps
Introduction to RemoteIoT Devices
RemoteIoT devices are intelligent systems designed to operate independently while maintaining connectivity with central networks. These devices are used in various applications, including environmental monitoring, healthcare, agriculture, and manufacturing. A key aspect of managing these devices is ensuring secure communication, which is where SSH comes into play.
In this section, we'll explore:
- What makes RemoteIoT devices unique
- Common applications of RemoteIoT devices
- Why security is critical for IoT deployments
Understanding the fundamentals of RemoteIoT devices will help you appreciate the importance of secure protocols like SSH in maintaining robust and reliable networks.
What is SSH?
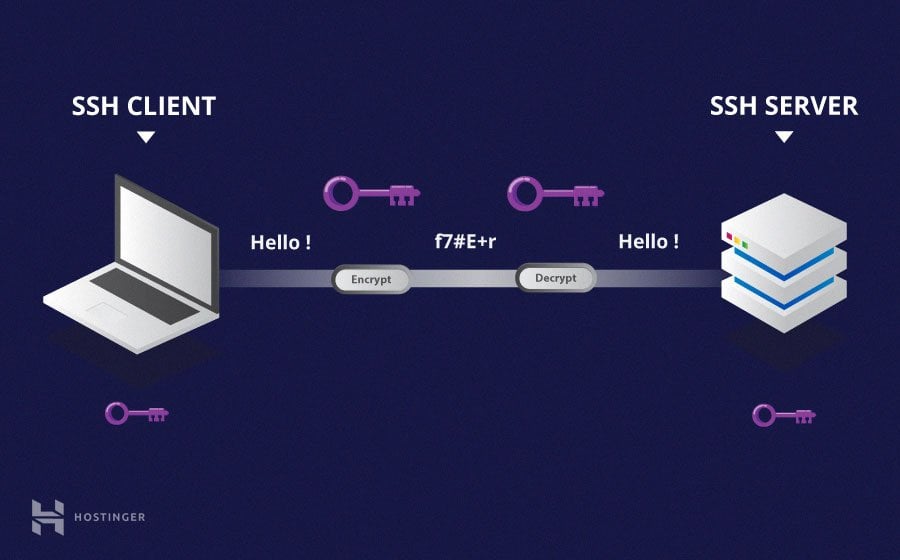
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication over unsecured networks. It is widely used for remote device management, file transfers, and command execution. For RemoteIoT devices, SSH ensures that all data exchanged between the device and the user is encrypted and protected from unauthorized access.
How SSH Works
SSH operates by establishing an encrypted connection between a client and a server. The process involves:
- Client-server authentication
- Key exchange for encryption
- Secure communication channel establishment
By leveraging SSH, you can confidently manage your RemoteIoT devices without worrying about data breaches or interception.
Read also:Aaron Carter And Diddy The Untold Story Of Their Connection
Setting Up a RemoteIoT Device
Before you can connect to a RemoteIoT device via SSH, you need to ensure that the device is properly configured. This involves:
- Installing the necessary firmware
- Configuring network settings
- Enabling SSH access
Refer to the device's official documentation for specific setup instructions. Most manufacturers provide detailed guides to help users get started with their IoT devices.
Connecting to a RemoteIoT Device via SSH
Connecting to a RemoteIoT device via SSH requires a few simple steps. Follow this guide to establish a secure connection:
Step 1: Install an SSH Client
Depending on your operating system, you may need to install an SSH client. Popular options include:
- OpenSSH (for Linux and macOS)
- PuTTY (for Windows)
Step 2: Obtain Device Credentials
You'll need the IP address, username, and password of your RemoteIoT device. These details are usually provided during the initial setup.
Step 3: Establish the Connection
Use the following command to connect to your device:
ssh username@device_ip_address
Replace "username" and "device_ip_address" with the actual credentials of your device.
Securing SSH Connections
While SSH provides a secure communication channel, additional measures can enhance its security. Consider implementing the following best practices:
- Use strong, unique passwords
- Enable two-factor authentication (2FA)
- Disable password-based authentication and use SSH keys instead
- Restrict SSH access to specific IP addresses
By following these guidelines, you can significantly reduce the risk of unauthorized access to your RemoteIoT devices.
Troubleshooting Common Issues
Even with careful setup, issues may arise when connecting to RemoteIoT devices via SSH. Here are some common problems and their solutions:
Problem: Connection Refused
Solution: Ensure that the SSH service is running on the device and that the firewall allows incoming SSH connections.
Problem: Authentication Failed
Solution: Double-check your username and password. If you're using SSH keys, verify that the public key is correctly added to the device's authorized_keys file.
Problem: Slow Connection
Solution: Optimize your network settings and consider using a faster internet connection.
Advanced SSH Configurations
For advanced users, SSH offers a range of configuration options to tailor the connection to specific needs. Some popular configurations include:
- Port forwarding
- Tunneling
- Custom SSH configurations in the ~/.ssh/config file
Refer to the official SSH documentation for detailed instructions on implementing these configurations.
Best Practices for RemoteIoT SSH Management
To ensure the long-term security and reliability of your RemoteIoT devices, follow these best practices:
- Regularly update firmware and software
- Monitor SSH logs for suspicious activity
- Limit SSH access to trusted users
- Perform routine security audits
Adhering to these practices will help you maintain a secure and efficient IoT infrastructure.
Use Cases for RemoteIoT SSH
SSH is a versatile tool with numerous applications in the realm of RemoteIoT devices. Some common use cases include:
- Remote device management
- Secure file transfers
- Automated system updates
- Real-time data monitoring
By leveraging SSH, you can unlock the full potential of your RemoteIoT devices and streamline your operations.
Conclusion and Next Steps
In this tutorial, we've explored the fundamentals of RemoteIoT devices and SSH, including setup instructions, security best practices, and advanced configurations. By following the steps outlined in this guide, you can confidently manage your IoT infrastructure and ensure its security.
We encourage you to:
- Practice the steps outlined in this tutorial on a test device
- Explore additional SSH features and configurations
- Stay updated with the latest developments in IoT security
Feel free to leave a comment below if you have any questions or suggestions. Don't forget to share this article with others who may find it helpful!
Sources: